Utilizar el Traductor de Google en la parte superior de la columna central
Utilisez Google Translate au haut de la colonne du milieu
Google’ın Orta Sütun Top of Çevir kullanın
Используйте Google Translate в верхней части среднего столбца
Sử dụng Google Translate Đầu Cột Trung
उपयोग Google मध्य स्तंभ के शीर्ष पर अनुवाद
在中间一列的顶部,使用谷歌翻译
04 CH 2.4 Information Pathologies 21-34
Book Master Page with All Chapters
DRAFT 4 OF 15
Chapter 2:
The InfoSphere & Its Enemies
Funded by John Dodson (TX) & Peter Thibault (ME)
A. Cybernetics 101 22
B. Truth or Not Truth 22
C. The Evolution of Information Needs 23
D. Eight Isolated Information Communities 24
E. Information Cube 25
F. Information Fragmentation 26
G. Information Pathologies 27
H. Sourcing – Art & Science 29
I. Collective Intelligence 29
J. The Human Factor – Always 30
K. Information Challenges 30
Reader’s Guide
Our world is a “system of systems” so complex that it is beyond the understanding of any one man, any one group, any one nation, even all of us together. In such a complex context, lies are like sand in the gears of a very delicate machine. Sometimes knowledge may be known but buried in a tsunami of advertising; it can be forbidden as some religions forbid certain texts and some nations forbid certain literatures. Knowledge can be lost, manipulated, or never revealed outside a select circle. Within larger systems such as global corporations and major nations, lies can be taken to a very sophisticated level, with intricate inter-locking lies creating a public perception far removed from the truth. This is the context for the emerging profession of public intelligence. To find the truth, one must first be able to identify every form of misdirection including extraordinary forgeries, lies from sources one would think impeccable, and very often, one’s own government – in the USA, for example, unemployment statistics are generally one third of the real numbers. Broken promises are a form of lie, one reason why trust built up over time is so precious. Every fact, every opinion, every observation, has a provenance, as with a work of art. Information Operations (IO) are defined by the constant interaction of the human factor, information pathologies, and institutional failures, with the all too rare community successes being achievements we must strive to replicate on the basis of transparency, truth, and trust.
A. Cybernetics 101
Put most simply, cybernetics is about feedback loops. Simple systems have single feed-back loops that are relatively easy to perceive and understand. Simple systems fail in simple ways that are relatively easy to perceive and correct.
Complex systems have complex feedback loops that cross over one another and are difficult to catalog and monitor. Complex systems fail in complex ways that often mutate or accelerate or otherwise modify the failure, and are very difficult to diagnose and repair (Perrow, 1999).
The Earth – and particularly the Earth as we do not understand it and as grievously affected by the Anthrosphere – the human influence with all its toxins – is a constellation of complex systems with feedback loops across at least four dimensions and perhaps as many as twenty-six.
The changes to the Earth, most being caused by the Anthrosphere but others associated with the Sun and other influences, is changing at an accelerating rate. Changes to the Earth that once took 10,000 years now take three or less (Perrow, 2011).
Information is the substance of all feedback loops – whether it is biological, chemical, analog, or digital. Information is also the substance of what we observe (first-order cybernetics); how that changes us and how we react to it all (second-order cybernetics); and finally, it comprises the “whole” of our multi-species co-existence and co-evolution with everything else (third-order cybernetics.
Intelligence (decision-support), when fully integrated of education (the human behavior unit), and research (the human observing unit), is the brain of any given community. Writ large, at global scale and only if we can implement Open Source Everything (OSE) and Multinational, Multiagency, Multidisciplinary, Multidomain Information-Sharing and Sense-Making (M4IS2), we are creating the World Brain and Global Game, a prosperous world at peace (Steele 2008).
B. Truth or Not Truth
The truth at any cost lowers all other costs. The purpose of intelligence is to arrive at the truth and present that truth to the decision-maker. The intelligence professional must be proficient at discerning all forms of information pathology that seek to corrupt, conceal, or pervert the truth.
Bob Seelert, Chairman of Saatchi & Saatchi Worldwide (New York): When things are not going well, until you get the truth out on the table, no matter how ugly, you are not in a position to deal with it.
In a world of constantly changing information, it is impossible for any structured organization to dominate a larger network—a hybrid network. Such broad, flexible governance without governments being “in charge” is where we need to go. The objective: to implement transparency, truth, and trust across all boundaries. (Conca 2005; Reinicke 1998, 2000; Rosenau 1992)
David Weinberger (2012) is a genius on this point: not only can no one person or even one organization or one country “know” what they need to know to make an informed decision, but if they fail to understand, respect, and “jack in” to the knowledge network with full transparency as the method and truth as the objective, they will make very bad decisions. Of course this does not address the issue of corruption, and the raw fact that most governments and corporations could care less about objective truths, seeking instead to optimize profits for the few at the expense of the many, but their ignorance is our advantage. That is why We the People must recommit ourselves to Open-Source Everything, its underpinnings (transparency and truth), and its outcome: trust you can bank on without a bank. (Steele 2012)
I will say that again in a different way: the persistent unethical and ignorant emphasis on secrecy and on making decisions for partisan advantage or to pay off campaign contributors and select insiders is not sustainable. We the People have an opportunity to embrace this manifesto of Open-Source Everything and bury “rule by secrecy.” This is this is why I am optimistic about the future.
C. The Evolution of Information Needs
Put simply, the evolution of humanity has passed through a physical phase that is now in retrograde (the obesity epidemic), a mental phase (still in infancy), and a spiritual phrase (hardly gestated but recognized by some). Below is a very general depiction of seven generations of information needs and wants, from a military perspective.
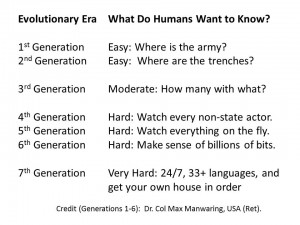
Figure 9. Seven Generations of Information Needs and Wants (Military Version)
In each of the above “generations” of information need and want, the humans did not know what they did not know and they generally did not know what they could know or needed to know beyond what was obvious to them.
A major – truly fundamental – reason for pursuing “all information in all languages all the time” (Steele 2008) while also pursuing the OSE/M4IS2 approach to intelligence, is to radically increase the diversity of information impressions on the maximum possible number of human brain sets.
D. Eight Isolated Information Communities
I developed a sense of the information continuum in the early 1990’s but it was not until Alvin Toffler and I were driving away from a lunch with some US military intelligence senior executives that he turned to me and said “they don’t want to leave their little green box.” That is when my understanding “clicked” and I created the below set of building blocks, all isolated from one another. In chapter 1, Figure 3 represents the ideal. Below, Figure 10 represents reality.
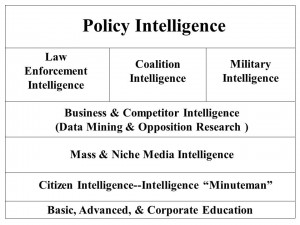
Figure 10. Eight Isolated Information Communities
Lacking development of page.
E. Information Cube
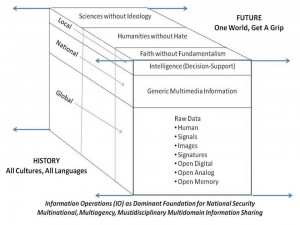
Figure 11. The Information Cube
Lacking development of page.
F. Information Fragmentation
This is illustrated below in Figure 2 which illustrates the fragmentation of the scientific disciplines and sub-disciplines.

Figure 12: Fragmentation of “Structured” Knowledge
Lacking development of page.
G. Information Pathologies
Fog Facts
These are facts that are “known” to some and publicly accessible but only if you know where to look. The mainstream media “blacks out” this knowledge. Modern examples include U.S. government support for dictators and U.S. government tolerance of massive fraud, waste, and abuse in return for fractional campaign contributions to presidential and legislative candidates who strive to remain in office “at any cost.” (Beinhart 2006)
Forbidden Knowledge
This includes both knowledge forbidden for public consumption by governments (e.g. restrictions on pornography) as well as corporations (e.g. concealment of known pathologies such as the effect of tobacco on cancer, or toxins associated with household goods) and religions (the triumph of dogma over consciousness). (Shattuck 1997)
Forgotten Knowledge
Knowledge is forgotten, without malice, but out of ignorance or nonchalance. The deepest form of forgotten knowledge is that of our indigenous forbearers such as the Mayans and of civilizations that existed prior to the commonly understood 2500 BCE era of Egypt, Greece, and Sumaria (Chouinard 2012, Hardy 2011, Mann 2006, Schock 2012).
Lost History
The most prominent modern example is the deliberate classification as secret of clandestine and covert operations by the U.S. government such that a modern history of foreign relations cannot be written—this is the documented complaint of the historians responsible for this task on behalf of the Department of State. (Weissman 2011). The role of the Central Intelligence Agency in the introduction of massive amounts of cocaine into the USA under the pretext of supporting “strategic” operations “at any cost” is especially frightening to anyone upholding the Constitution. (Parry 1999, Webb 1999) One also has the matters of the assassinations of John F. Kennedy and Martin Luther King with the complicity of elements of the U.S. Government, and then their cover-up – and the Israeli attack on the USS Liberty, an attack that was covered up for decades with the survivors told they would lose their pensions if they spoke of the attack on our unarmed ship by unmarked Israeli aircraft and patrol boats.
Manufacturing Consent
Noam Chomsky and Edward Herman (2002) first discussed this aspect of a modern democracy, and now, decades later, their work has been updated by Sheldon Wolin in his book, Democracy Incorporated: Managed Democracy and the Specter of Inverted Totalitarianism. (2010) Corporations now “own” not just the legislative and executive branches of the U.S. government, but the judiciary as well, with the Supreme Court ruling on Citizens United being the more reprehensible evidence of the corruption of the highest court in the nation.
Missing Information
Bill McKibben (2006) did something never done before—he recorded all the television channels being broadcast in his area in one twenty-four-hour period, and watched them all over the course of time. He then spent twenty-four hours alone in the wilderness. Comparing the two experiences, he produced a truly brilliant exposition of how much “missing information” there is in our lives.
This is a distinct challenge from that created by the chasms between human knowledge not recorded, analog or limited edition knowledge, and digital knowledge lost in the cyber-caverns.
Propaganda
Propaganda, put most simply, is the development of manipulated (i.e., not truthful) information and the delivery of that information to an audience in such a way as to impress upon them views and beliefs that are not rooted in fact or deliberative dialog. Propaganda, which includes advertising that itself fosters an appreciation for planned obsolescence, waste, and toxic foods and goods, is the antithesis of transparency, truth, and trust. (Ellul 1973)
Rule by Secrecy
(Marrs 2001) As we have all now realized, and as Occupy is now confronting on Wall Street and around the world, secret banking networks, not governments, have been making decisions about war and peace, poverty and prosperity. It is banks that profit most from wars, followed by the military-Industrial-congressional complex (MICC), and We the People that suffer most. Government secrecy enables massive lies—such as the 935 documented lies delivered by Dick Cheney that took us into a multi-trillion dollar losing war in Iraq (Lewis and Reading-Smith 2008)—and this is one reason why I have committed the balance of my life to Open-Source Everything: transparency, truth, and trust are the true currency for human transactions – everything else is a cancer. (Steele 2012)
Weapons of Mass Deception
(Rampton and Stauber 2003) Whereas Rule by Secrecy is about secret cabals making decisions on the truth as they know it, Weapons of Mass Deception are about blatant lies—many of them allowed to go unchallenged by the media, think tanks, university specialists, and all others who should be thinking in the public interest but instead choose to “go along” out of a selfish and unethical dependency on funding from the government doing the lying. A form of mass hysteria is achieved, one best illuminated by the manner in which the three singers of the band Dixie Chicks, were treated when they publicly protested and questioned the veracity of the White House.[1] Now, years later, as with Jane Fonda on Viet-Nam, we know that the White House was committing treason, and the Dixie Chicks were both ethical and correct in their protestations. Mass hysteria – and mainstream media corruption – prevented the broader public from recognizing the truth at the time.
Weapons of Mass Instruction
(Gato 2010). Underlying the ability of a treasonous White House and a complicit Congress (which must abdicate its Article 1 responsibilities when going along with known lies to permit an undeclared war at great cost) is a national educational system that is at best mediocre and at worst a crime against humanity. We are imposing on children of the Internet era—digital natives—an industrial-era system that is mindless: rote learning of old knowledge, sitting silent for hours on end, listening to lectures best left silent and so easily replaced by more vibrant multimedia communications. Teachers and the educational stakeholders who are complicit in the criminally negligent continuation of a retarded educational system are a foundation for an uninformed, unengaged public. (De Coster 2012)
H. Sourcing – Art & Science
Every source has a provenance, just as art works have provenances. Virtually nothing published by anyone can be accepted at face value. The challenge of validating sources has gotten so great for those who are not intelligence professionals that TIME Magazine has given up on fact checking! (Hart 2012)
A major failing among those who pretend to be expert at anything is their lack of real knowledge about source discovery and validation, particularly outside their primary discipline and beyond their tribe.
Being able to understand, at a contextual, cultural, ethnic, historical, religious, and tribal level, any given source—to understand the humans that underlay all sources, to be able to discriminate among sources and create a mosaic that can be vouched for in relation to the requirement being met, is one of the greatest challenges facing the intelligence professional. It is not the only challenge. Having a strategic analytic and collection management model, knowing who knows, being able to leverage badly designed information technologies without losing sight of the human factor, being able to explain complex issues to busy decision-makers who can understand just three colors (red, yellow, green)—all these challenges make the profession rewarding. Sourcing is the mosaic of complexity we must master.
I. Collective Intelligence
Much has been written about how mass collaboration—alternatively called Smart Mobs (Rheingold 2003); Wisdom of the Crowds (Surowiecki 2005); Army of Davids (Reynolds 2007); Collective Intelligence (Tovey et al 2008); Here Comes Everybody (Shirky 2009)—has not been possible in complex situations in the past because the industrial era introduced (imposed) a cumulative series of information pathologies that deprived the group of access to all relevant information, while favoring an elite few with privileged access that allowed them to concentrate both power and wealth. In the public domain, many artificial—that is to say, contrived—obstacles to informing the public have prevailed in the past century, such as the following:
New, open-source, populist-based, information-era strategies will also serve our increasingly complex lives better in future situations of crisis such as natural disaster, war, and social disintegration. Collapse is cultural, systemic, a failure of process, not of any discrete event, institution, or location. The industrial-era model of command and control cannot adequately process information for a complex system, but an information-era model of distributed localized resilience can.
Collaboration and consensus is the Epoch B way, but from the philanthropic foundations to the non-governmental organizations to all others, there is still a dearth of information-sharing that is both expensive and incapacitating. While the United Nations has committed itself to coherence, with the meme of “Deliver As One,” they do not have the intelligence—or the integrity—to actually do that. Similarly, governments talk of “whole of government” operations, and corporations of “matrixed management,” but these also fail the intelligence and integrity tests.
J. The Human Factor – Always
Nature does not lie. Machines do not lie. Only the human can conceive of and deliver lies. The human, even when organized, is still, today, out of touch with all information in all languages.
The social sciences are hardly scientific, and the humanities have their blessed forms of incoherence. Science, philosophy, and religion continue to have difficulty mixing, although there has been more attention recently, to the possibility that science and religion might be striving to seek truth, each in their own way, in such a manner as to advance society in both scientific and spiritual terms. (Kung 2008, Molben 2011, Polkinghorne 2009).
Certainly the philosophers have felt for centuries that education is fundamental, and that the primarily role of the humanities is to save science from itself (Durant 1916, Wilson 1999).
K. Information Challenges
Each level of intelligence has its own challenges, just as each discipline and domain presents unique challenges in time, space, language and medium.
At the strategic level, we are at the end of an Industrial Era in which corruption has led to both doing and buying the wrong things, such that an average of 50 percent of every federal dollar is fraud, waste, or abuse. From agriculture to education to energy to health to the military – an average of 50% is fraud, waste, or abuse – and the other 50% creates toxins, exports jobs,
At the operational level, again as a result of pervasive corruption (both intellectual and financial), we are optimized for unilateral operations, and then generally only with the military – the other Cabinet departments are not trained, equipped, nor organized to “surge” overseas.
At the tactical level, our individual unit agility and capability is not supported by intelligence or communications, and we generally cannot bring fires to bear in direct support of small units in any kind of affordable and sustainable manner.
At the technical level, fifty years of failing to invest in human speaking 183 foreign languages, and also failing to invest in machine processing of all source information (that still does not have geospatial attributes associated with every datum); and fifty years of ignoring open sources and focusing exclusively on secret hard target sources, have left us virtually blind, deaf, and dumb.
TERMS OF REFERENCE
| Abuse | Fact | Philosophy |
| Analysis | Forbidden | Processing |
| Analytic Model | Forgotten | Propaganda |
| Authentic | Fraud | Religion |
| Collaboration | Human Factor | Rote Learning |
| Collection | Humanities | Science |
| Consensus | Indigenous | Smart Mob |
| Context | Instruction | Sub-Discipline |
| Corruption | Language | Time |
| Deception | Lost | Truth |
| Discipline | Patriotism | Waste |
READINGS
Beinhart, Larry (2006). Fog Facts: Searching for Truth in the Land of Spin. New York, NY: Nation Books.
Chouinard, Patrick (2012). Forgotten Worlds: From Atlantis to the X-Woman of Siberia and the Hobbits of Flores. Rochester, VT: Bear & Company.
Ellsberg, Daniel (2003). Secrets: A Memoir of Vietnam and the Pentagon Papers. New York, NY: Penguin.
Ellul, Jacques (1973). Propaganda: The Formation of Men’s Attitudes. New York, NY: Vintage.
Gaddis, J.L. (2004) The Landscape of History: How Historians Map the Past. Oxford, UK: Oxford University Press.
Gatto, John Taylor (2010). Weapons of Mass Instruction: A Schoolteacher’s Journey Through the Dark World of Compulsory Schooling. Gabriola, BC: New Society Publishers.
Gilad, Ben (1991). Business Blindspots: Replacing Your Company's Entrenched and Outdated Myths, Beliefs and Assumptions With the Realities of Today's Markets. Probus Professional Publications.
Hardy, Karen (ed.) (2011). Archaeological Invisibility and Forgotten Knowledge: Conference Proceedings, University of Lodz, Poland, 5th7th September 2007. Oxford, UK: British Archeological Reports.
Hart, Peter (2012). “Time Gives Up on Factchecking: Corporate media can’t find a way to tell the truth.” Fairness & Accuracy in Reporting, 1 December.
Hiam, Michael (2006). Who the Hell Are We Fighting?: The Story of Sam Adams and the Vietnam Intelligence Wars. Hanover, NH: Steerforth.
Herman, Edward and Noam Chomsky (2002). Manufacturing Consent: The Political Economy of the Mass Media. New York, NY: Pantheon.
Mann, Charles (2006). 1491: New Revelations of the Americas Before Columbus. New York, NY: Vintage.
Marrs, Jim (2001). Rule by Secrecy: The Hidden History That Connects the Trilateral Commission, the Freemasons, and the Great Pyramids. New York, NY: William Morrow.
McKibben, Bill (2006). The Age of Missing Information. New York, NY: Random House.
Parry, Robert (1999). Lost History: Contras, Cocaine, the Press & ‘Project Truth’. Chicago, IL: Media Consortium.
Perrow, Charles (2011), The Next Catastrophe: Reducing Our Vulnerabilities to Natural, Industrial, and Terrorist Disasters (Princeton, NJ: Princeton University Press).
Perrow, Charles (1999), Normal Accidents: Living with High-Risk Technologies (Princeton, NJ: Princeton University Press).
Priest, Dana and William M. Arkin (2012). Top Secret America: The Rise of the New American Security State. Back Bay Books.
Rampton, Sheldon and John Stauber (2003). Weapons of Mass Deception: The Uses of Propaganda in Bush’s War on Iraq. New York, NY: Tarcher.
Schoch, Robert (2012). Forgotten Civilization: The Role of Solar Outbursts in Our Past and Future. Rochester, VT: Inner Traditions.
Scott, James (2010). The Attack on the Liberty: The Untold Story of Israel's Deadly 1967 Assault on a U.S. Spy Ship. New York, NY: Simon & Schuster.
Shattuck, Roger (1997). Forbidden Knowledge: From Prometheus to Pornography. New York, NY: Mariner Books.
Webb, Gary (1999). Dark Alliance: The CIA, the Contras, and the Crack Cocaine Explosion. New York, NY: Seven Stories Press.
Weinberger, David (2012). Too Big to Know: Rethinking Knowledge Now That the Facts Aren't the Facts, Experts Are Everywhere, and the Smartest Person in the Room Is the Room, New York, NY: Basic Books
Zegart, A.B. (2009). Spying Blind: The CIA, the FBI, and the Origins of 9/11. Princeton, NJ: Princeton University Press.
ASSIGNMENT
At Amazon, find and read one substantive review for each of the books above. Active links to each book’s Amazon page can be found at the Online Resource Center where all readings are posted in both chapter and alphabetical order.
QUESTIONS
1. What is the truth and why does it matter?
2. America went to war on Iraq on the basis of 935 now-documented lies. Discuss.
3. John Deutch, then Director of the CIA, claimed to have no knowledge of CIA being the force behind Contra drug shipments that led to the crack cocaine explosion. I believe him. Discuss.
4. In 1990 everyone was upset with Winn Schwartau, Robert Steele, and a few others including Air War College officers, who documented vulnerabilities in US financial, telecommunications, and utility systems. Today those vulnerabilities still exist. Discuss.
5. Discuss the USS Liberty as an instance of now-documented cover-up. What might be the long-term effects of both the attack and the cover-up on US-Israel relations and specifically on US public and US military trust – or lack of trust – for any claims made by Israel?
6. Select any mass shooting in the USA or elsewhere, and evaluate how well the shooting was reported in the media, in blogs, and by other means.
7. What are the sources of any adult’s continuing education? How important or unimportant is it that those sources cannot be relied upon to report the objective truth? What are the alternatives for a citizen desiring to be fully and reliably informed?
[1] During a London concert ten days before the 2003 invasion of Iraq, lead vocalist Maines said “we don’t want this war, this violence, and we’re ashamed that the President of the United States (George W. Bush) is from Texas”. The statement offended many Americans, who thought it rude and unpatriotic, and the ensuing controversy cost the band half of their concert audience attendance in the United States. The incident negatively affected their career and led to accusations of the three women being “un-American”, as well as to hate mail, death threats, and the public destruction of their albums in protest. Source: Wikipedia/Dixie Chicks, with many linked citations.



