
Thomas Leo Briggs is a retired CIA operations officer with 3 years military experience in US Army military police, 3 years as a Special Agent in the Drug Enforcement Administration and 26 years in the CIA. He tried to make use of computer capabilities to aid and assist HUMINT operations in a variety of ways throughout his last 18 years as an operations officer. He is also the author of Cash on Delivery: CIA Special Operations During the Secret War in Laos (Rosebank Press, 2009).
– – – – – – – – – – – – –
Further reflection on HUMINT and OSINT. I see them as complementary to both operations (HUMINT collection) and analysis. I also see that they should be looked at differently for operations and analysis.
In operations, which I know more about than analysis, there is the general need for HUMINT operators (so as to not bias this toward any one member of the intel community, I use HUMINT operators rather than case officers) to know as much as as possible about the country, region, culture, etcetera where they will be working. Operators collect raw intelligence and it is turned into field intelligence reporting. Someone in the field must review and vet that raw intelligence – we used to call them reports officers. The review must be able to determine if the alleged raw intelligence is really that and not openly known information somewhere in the country or region. Obviously, there must be one or more officers in a field office with knowledge of as much about the open source information as possible, or has the tools at hand to check open source information, and also with knowledge of the secret intelligence that has already been reported, so as to avoid duplicative raw intelligence reporting.
It would certainly help if HUMINT operators either knew or could check open source information against what was being collected, but in my experience, very few want to do that or even try. Thus the need for the officer through whom the raw intelligence must pass for review before it leaves the field office. This is one option for the use of open source information in HUMINT collection.
However, I would also make an argument for the use of open source information to directly aid HUMINT collection. Here is one possible scenario for the complementary use of HUMINT and OSINT.
Suppose your HUMINT collection requirement is for intelligence on bad actor nations' developing of weapons of mass destruction. Further, you have open source information that scientists from bad actor nations are permitted to leave their countries to participate in scientific projects at universities and other research facilities around the world, including the United States. Not only may they leave their countries but they are also welcomed to become part of scientific teams in university and other research programs all over the world.
Here you have the target environment for identifying scientists from bad actor nations and possibly targeting them for recruitment. You also have, among the other scientists in the research project, possible targets for recruitment as access agents.
Next, you learn that all the scientific research teams publish open papers about their projects and these papers may be purchased in digital format from various publishers, e.g., Scientific Research Publishing and Reed-Elsevier.
These openly published papers describe the research and name the members of the research team, to include the scientists from the bad actor nations. Bad actor nation scientists participate in biological, chemical and nuclear research and can use the knowledge learned to return to their home countries and use it to aid the development of weapons of mass destruction.
The various weapons of mass destruction require knowledge of precursor technology in order to develop the weapons. A scientist may acquire precursor technology while working on chemical, biological or nuclear projects that are not aimed at weapons development. However, when you have the combination of bad actor nation scientist and research that includes researching precursor technologies, you have the possibility of those scientists returning home to contribute to weapons development.
Obviously, bad actor nation scientists don't advertise their intention to focus in on any of the various pieces of knowledge needed in the development of weapons of mass destruction and the research papers don't seem, on the surface to be aimed at weapons. Indeed, the research seems on the surface rather benign. Moreover, a human being, with knowledge of precursor technology in each of the three fields, would need to read every paper.
Next, let's consider you might be able to interview the leading intelligence analysts following the development of weapons of mass destruction and ask for a list of precursor technologies for the development of each type of weapon, e.g., someone from a bad actor nation acquiring knowledge about heavy water production might be suspected of wanting to take that knowledge home for weapons development.
Up to this point, you have not used much, if any, secret intelligence.
If you are going to purchase large quantities of digital information you will need a computer application capable of taking in the data and helping you analyze it. You have to purchase large quantities because the data is not conveniently sorted out so you can purchase only that data that has information about weapons of mass destruction precursor technology.
The data is available for purchase and the computer applications exist. You need only put them together, analyze them and produce a list of scientists. Next comes the first definitive use of secret information. You need to get background information on each scientist working on research that exposes bad actor nation scientists to weapons of mass destruction precursor technology.
Depending on the results of the background information requests you may now have bad actor nation targets for recruitment and targets for recruitment of access agents. You can also use open source information to study and analyze the operational environment of the research institute in order to insert other access agents or HUMINT collectors to penetrate the research teams.
There is more to be said about the use of computer applications and background information requests, but the intent of this is to merely describe how open source information is a very necessary complement to humint collection and without which, you could not hope to achieve any results in identifying bad actor nation scientists abroad in the free world and then run recruitment operations against them.
If you don't believe that would be a very worthwhile objective then you wasted your time reading this far.
I also submit that putting the above idea into action is not easy at least for all the jurisdictional boundaries needed to be crossed and all the “not invented in my back yard” obstructions, the most significant of which is “not invented in my back yard” usually provokes ignoring the idea and usually never gets support from above that insists that it be implemented.
This is one possible intersection of open source information and HUMINT collection. I am confident there are others.

Click Here to See Personal Page
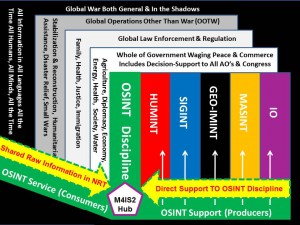
ROBERT STEELE: First, two contextual items. One, the clandestine stations under official cover are under very low burn times, and the best case officers, as in my case, go from station to station without wasting time at HQS (that does, however, kill your promotion prospects). They do not “read in” anywhere, and they are not expected to know anything substantive, just how to elicit and then type up, typing being one of the most important skills in the clandestine service. Second, the reason I have been calling for the clandestine service to vacate official cover premises (apart from the fact that it is blown and can be replaced by one declared liaison officer) is that I would like to put in a small inter-agency cell of all-source analysts, with an open source acquisition manager and a financial clerk. This is the vision that Doug Naquin simply could not comprehend, and that the CIA clandestine service refused to embrace because they LIKE living immunity rather than cover. I only had one small shot at success within CIA (this was after I left, while I was with the Marines. When Jack Devine was Chief of the Latin America Division in CIA/DO, I tried to get him to create an OSINT cell that would do spotting and assessing for the various missions in the Objective Memorandum for each Station in his division. It never happened for various reasons, not least being that Reports Officers have no clue how to do OSINT, and then as now, the CIA OSINT mafia — the once great Foreign Broadcast Information Service and the now mediocre Open Source Center — were not serious about a) being in touch with all open sources in all mediums and languages and b) putting someone in the field where they might have to sweat and endure dealing with foreign nationals. Those that have sought to leverage OSINT in support of HUMINT and Counterintelligence (CI) have done very well. The Royal Canadian Mounted Police and Scotland Yard, followed by EUROPOL (briefly) are stunning success stories. Informants validated, context provided for close in technical target selection, the list is long. And of course we have Arno Reuser, perhaps the single greatest and most effective pioneer at my own concept, “do not send a spy where a schoolboy can go.” Arno has done more with OSINT in support of EACH secret collection discipline, not just HUMINT, than anyone can imagine. In the Special Operations community, I helped pioneer Black OSINT — OSINT so good we could not reveal we were getting it or the source mix would dry up. A revolution is occurring in the world of intelligence (decision-support), and those who resist innovation now that there is no longer a surplus of money to carry non-hackers along, should be the first to feel the pain. It's time for US intelligence to come relevant, compelling, and profitable — information costs money, intelligence makes money. DoD strategy, policy, acquisition, and operations all lack decision-support because CIA and DIA are bureaucracies on auto-pilot and no one holds them accountable for being persistent failures. In my humble opinion.
See Also:
2006 Sutton (US) Global Coverage, Looking Backward, Looking Forward
2006 Reuser (NL) on Virtual Open Source Agency
2003 Reuser (NL) on Intelligence Librarian Tradecraft
2003 Markowitz (US) Open Source in Support to All-Source Intelligence
1999 Edwards (UK) Scotland Yard SO11 Open Source Unit Presentation



