
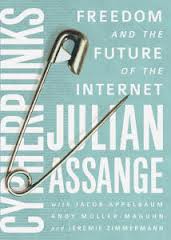
Book of the Day: Cypherpunks on Freedom and the Future of the Internet
Excerpted from a review by Cryptome:
“This is a highly informative book, perhaps the best published on the substance of WikiLeaks, its technology, philosophy, origin and purpose, rooted in the Cypherpunks resistance to authority through encryption and anonymizing technology. The trenchant and salient, wide-ranging discussion among Assange, Appelbaum, Müller-Maguhn and Zimmermann, is derived from a four-part RT series with additional editorial material and a summarizing prologue by Assange, “A Call to Cryptographic Arms.”
It is an excellent introduction to the struggle for control of digital communications, economics and governance. A prime candidate for inclusion of reading lists of the enemies of authoritarian institutions, corporations and governments heavily invested in the Internet and aiming to control it by secret collusion for their purposes — at the global public’s expense, loss of privacy and reduced democracy. It claims to be a “watchman’s warning” against the threat posed by the Internet and cellphone technology.
The panel asserts [11 points in all]:
1. The internet is a threat to human civilization because of its panoptic surveillance and profiling of users.
2. “Strategic surveillance” gathers all online and cellphone data as distinguished from tactical surveillance with is specifically targeted.
3. Internet and cellphones allow surveillance more efficiently and pervasively than in the physical world.
4. Individuals can be surveilled more easily if they remain mesmerized by computers, cellphones and social media.
5. Encryption prevents access to private secrets by official and commercial online surveillance and by cellphones.
6. Protestors in Arab Spring went to the streets when cellphone and online systems were disabled and thereby escaped digital surveillance.
7. General purpose computers avoid the built-in controls of special purpose computers and devices.
8. Free software avoids the control of restrictive governmental and commercial software.
9. Free encryption and anonymizing technologies can protect against authoritarian aggression embedded in the equipment and operating systems of computers, cellphones, networks, internet service providers, financial institutions and governments.
10. Younger generations will need to invent and distribute ideas, critiques, code and technology against the legacy controls of older generations indoctrinated in submissive acceptance of authority.
11. Diverse, heterogenic concepts and technology will be required to oppose centralizing, homogenizing intents of the government- and commerce-dominated Internet and cellphones.
Evgeny Morozov and other net-negativists may scowl at the blind faith in encryption and anonymizing technology to save the Internet for its all too gullible users. Some cypherpunks are appalled at what WikiLeaks and Assange have become through excessive publicity and promotion by supporters and opponents.
The book could be seen as a compendium of what not to do about communications security, privacy, secrecy and authoritarianism — for that it is to be studied carefully.
For me, the greatest virtue of this book is its description of what comes after the lessons learned of Cypherpunks and WikiLeaks — from the diverse initiatives nobody yet knows about due to deliberate avoidance of preening, crippling publicity.”



