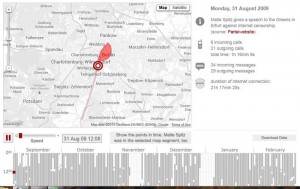
Activity-Based Intelligence Uses Metadata to Map Adversary Networks
Gabriel Miller
Defense News, 8 July 2013
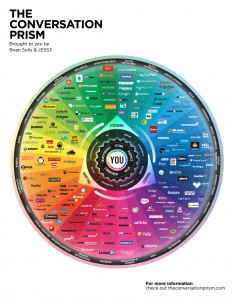
Few outside the intelligence community had heard of activity-based intelligence until December, when the National Geospatial Intelligence Agency awarded BAE Systems $60 million to develop products based on this newish methodology. But ABI, which focuses not on specific targets but on events, movements and transactions in a given area, is rapidly emerging as a powerful tool for understanding adversary networks and solving quandaries presented by asymmetrical warfare and big data.
Indeed, ABI is the type of intelligence tool that could be applied to the vast wash of metadata and internet transactions gathered by the NSA programs that were disclosed in June by a whistle-blower.
Full story below the line.