Re-Published with Permission. See Ben Garrison @ Phi Beta Iota
Stephen E. Arnold: Palantir Round-Up
IO Impotency
Palantir Round Up: The Beyond Search Commentary
Two Palantir Profiles: Some Peculiar Omissions
Phi Beta Iota: A crummy over-marketing offering that should not be considered by the Pentagon or anyone else. Bloated overhead that is beneath contempt and results that should outrage any serious customer.
See Also: Palantir @ Phi Beta Iota
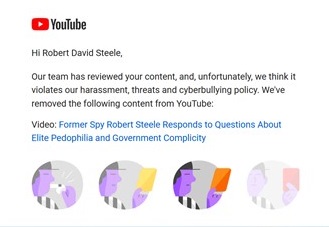
Paul Adams: Google & YouTube Sued — Restraining Order Sought
Commerce, Corruption, IO Impotency
Google and YouTube Sued for Censorship
Spurred by Whistleblower Revelations Big Tech Must Answer in Court Pre-Election TRO Sought
Working with Zach Vorhies, the Whistleblower who revealed Google’s 12 member “Hate Speech Committee” (half of whom are Red Chinese Nationals) the lawsuit alleges massive and systemic violations of Section 230 of the Telecommunications Act, the companies’ terms of contract and Freedom of Speech with regard to centrist, conservative and libertarian opinion communications.
74-Page Complaint & Video Explaining Lawsuit Below the Fold
Continue reading “Paul Adams: Google & YouTube Sued — Restraining Order Sought”
Mongoose: Addressing Big Tech Censorship — End Government Subsidies and Government Tolerance of Censorship & Manipulation
IO Impotency There Is A Solution To Big Tech Censorship – But No Politician Will Touch it
There Is A Solution To Big Tech Censorship – But No Politician Will Touch it
Social media and big tech do in fact represent a monopoly, but not in terms most people are familiar with. Instead of acting only as an economic monopoly controlling market share, big tech is also a political monopoly controlling the majority of communication platforms. If only one political and social ideological group dominates every major social media and digital information outlet, this in my view represents a completely unbalanced power dynamic that does indeed threaten the free speech rights of the populace.
Alastair Crooke: US Losing the S&T / Digital Standards War to China, Iran, & Russia
Advanced Cyber/IO, Autonomous Internet, Commercial Intelligence, IO ImpotencyThe Two Undersides to Geo-Politics
The prize that America truly seeks is to seize for itself over the coming decades, all global standards in leading-edge technology, and to deny them to China.
China’s intent now is not simply to refine and improve on existing technology, but to leapfrog existing knowledge into a new tech realm (such as by discovering and using new materials that overcome present limits to microprocessor evolution).
Penguin: Twitter Investigation Report
IO ImpotencyReport on Investigation of Twitter’s July 15, 2020 Cybersecurity Incident and the Implications for Election Security
Given that Twitter is a publicly traded, $37 billion technology company, it was surprising how easily the Hackers were able to penetrate Twitter’s network and gain access to internal tools allowing them to take over any Twitter user’s account. Indeed, the Hackers used basic techniques more akin to those of a traditional scam artist: phone calls where they pretended to be from Twitter’s Information Technology department. The extraordinary access the Hackers obtained with this simple technique underscores Twitter’s cybersecurity vulnerability and the potential for devastating consequences. Notably, the Twitter Hack did not involve any of the high-tech or sophisticated techniques often used in cyberattacks–no malware, no exploits, and no backdoors.