The ‘electronic Pearl Harbor’
Eighteen years ago I was the first to use that term publicly. It was the wrong analogy then. Not anymore.
The phrase became a touchstone in the long national argument over cybersecurity, for better or worse. I was not the author of the phrase. That honor goes to a dear friend of mine, retired U.S. Air Force Gen. Tom Marsh, who had just led a national commission looking at cyber vulnerabilities. Tom came to my office to summarize the findings and used the Pearl Harbor metaphor.
ROBERT STEELE: John Hamre means well, but this is a double failure of integrity. First, Politico evidently does not bother to fact check anymore (at the same time that they block legitimate commentators who do know the facts, from posting comments). So good-bye, Politico, not worth a bucket of warm spit when it comes to the facts. Second, we are stunned to see John Hamre accepting a term from a national commission as their own without bothering to inquire as to who actually originated the term: Winn Schwartau, informally from 1988 when he wrote Terminal Compromise, formally to Congress in testimony on 26 June 1991 where he was blown-off by know-nothing Members and staff . Few people know that it was Robert Steele who sounded the alarm officially to the White House, after Winn had first testified to Congress, and even fewer know that the anonymous co-signer of the letter to the White House via the Treasury action officer was James Anderson, at the time NSA's “top gun” for communications and computing security concerns. Not many — including John Hamre — know that the U.S. Air War College excelled from 1990-1994 at studying the vulnerabilities across all financial, power, communications, and other systems — including SCADA or Supervisory Control and Data Acquisition systems. This was not something the chain of command cared about and it was never anything DoD “leaders” wanted to discuss, in part because it was not an expensive enough problem and the Congressional pork machine was simply not interested. I opened Hackers on Planet Earth (HOPE) in 1994 at Winn's suggestion, and have spoken at every conference since. I am an elected member of the Silicon Valley Hackers Conference started by Stewart Brand and now managed by Glenn Tenney. My bottom line: neither the US Government nor mainstream US information technology companies have a clue. The Internet sucks, in part because We the People are too willing to be distracted by crap.
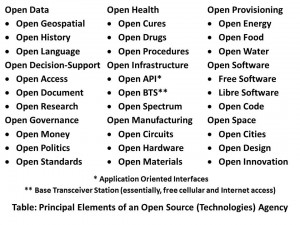
Worse, we now know that when NSA was ordered to secure US commercial communications and computing capabilities, they chose instead — with the full and active complicity of the CEOs of major firms including Dell, HP, IBM, and Microsoft — and more recently Google — to create infantile back doors that literally created the Russian and Chinese hacking industries and incentivized a marketplace that did not exist in substantive form prior to NSA's culpable criminally irresponsible treason. I have called for the termination of the DNI, NRO, NSA, and NGA, this includes the Cyber-Command that may be the most expensive and also the stupidest element of the US Government in relation to its puported responsibilities. Cyber-security must go to the new Open Source (Technologies) Agency and its Applied Collective Intelligence elements and we must embrace — and take the lead on — decentralized blockchain technology that cannot be undermined by corrupt officials in both public and private service. Neither the US secret intelligence community nor the bloated wasteful pathological dysfunctional Department of Defense protect the USA — they make everything worse. Giving more money to institutions that are documented as being 45% to 75% waste is criminally insane and illustrative of the profound ignorance of most of the so-called presidential candidates, Donald Trump and Mario Rubio particularly. Those that know better, such as John Kaisch and George Pataki, have been eclipsed by what Christopher Hedges so able described in his book, Empire of Illusion: The End of Literacy and the Triumph of Spectacle. Add to that Matt Taibbi's Griftopia: Bubble Machines, Vampire Squids, and the Long Con That Is Breaking America. Ted Cruz seems to stand out at the intersection of integrity, sensibility, and viability, but I personally do not believe 2016 is going to be won by anyone who persists in a single party winner take all strategy — we need multiple national conversations between now and then, on the Constitution, on electoral reform, on the gutting of an out of control federal bureaucracy that was never intended to be “above” the States.
If we are to make America safe again, we need to agree on the threats that face us; agree on a grand strategy and then a force structure, and finally we need to agree that corruption and waste are unpatriotic and unacceptable across the national security as well as the domestic well-being domains.In addition to shutting down two thirds of the mass surveillance secret world that is both useless and expensive, I believe we must close all our bases overseas, reuniting families here at home by bringing back our troops and their wallets, while creating a 450 ship Navy (the CNO agrees with me 22 years after I was almost fired for this excellent idea), a long-haul Air Force, and an air-mobile Army that takes over the Close Air Support (CAS) mission. My thoughts on defense reconstructions are at Amazon, in An American Grand Strategy: Evidence-Based, Affordable, Balanced, Flexible. Those who prefer a word document can find it online at Phi Beta Iota, or can send me an email visible at my personal website, http://robertdavidsteele.com.
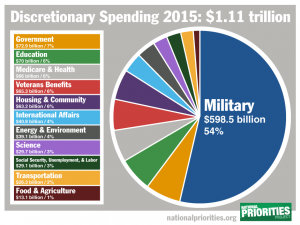 There is a great deal of work to be done. We are not well served when posers are not fact-checked. Sadly, what passes for “fact-checking” these days strikes me more as infantile interns operating with impunity — Politico was irresponsible with this post by Hamre; the post should be left up but corrected in a responsible manner. I have suggested to Politico that they could reasonably be expected to interview the four original authors of the original letter to the White House: Winn Schwartau, Bill Caelli, James Anderson, and myself. CNN has not covered itself with glory either. Anyone stupid enough to seriously suggest they would add money to a Department of Defense that already consumes 60% of the disposable budget in 2015, 16% of the total budget, should be pied out of office.
There is a great deal of work to be done. We are not well served when posers are not fact-checked. Sadly, what passes for “fact-checking” these days strikes me more as infantile interns operating with impunity — Politico was irresponsible with this post by Hamre; the post should be left up but corrected in a responsible manner. I have suggested to Politico that they could reasonably be expected to interview the four original authors of the original letter to the White House: Winn Schwartau, Bill Caelli, James Anderson, and myself. CNN has not covered itself with glory either. Anyone stupid enough to seriously suggest they would add money to a Department of Defense that already consumes 60% of the disposable budget in 2015, 16% of the total budget, should be pied out of office.
Robert James Beckett and I have agreed that we are departing the information age and entering the era of ethics, truth, and virtue. My personal motto is “the truth at any cost lowers all other costs.” I am inspired by a handful of people that actually “get” that such as Bob Seelert, CEO of Saatchi & Saatchi Worldwide, who says, When things are not going well, until you get the truth out on the table, no matter how ugly, you are not in a position to deal with it. It's time our Presidential candidates reconnected with the facts and their integrity. Hamre, and Politico, are the poster children for why we get it wrong so often.
See Especially:
1990-2014 Steele on Specific Intelligence Reforms (Including Alarm on NSA from 1994 Onwards)
Berto Jongman: cyber pearl harbor panel discussion – 22 Years Late
Criminally insane irresponsibility led to modern ‘hacker’s paradise’
DefDog: Is DHS Stupid, Dishonest, or Both? + RECAP
Journal: Army Industrial-Era Network Security + Cyber-Security RECAP (Links to Past Posts)
SCADA Vulnerabilities–Known Problem Since 1990
Winn Schwartau: From Electronic Pearl Harbor to Hactivism
See Also:
Cyber-Security @ Phi Beta Iota
Winn Schwartau @ Phi Beta Iota