Attached herewith is an essay I just wrote for Counterpunch.
For you convenience I have also attached a very important McClatchy report on the Orwellian Insider Threat Program being promoted by the Obama Administration.
The lead co-author, Jonathan Landay, is one of the few mainstream reporters who has been onto the lunacy unleashed by 9-11 from the git go.
My intent in the essay is to place this dangerous craziness in a somewhat larger larger context of our morally and mentally bankrupt intelligence system … judge for yourself whether or not I have been successful.
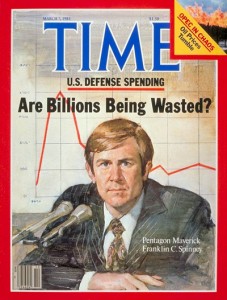
by FRANKLIN C. SPINNEY, Counterpunch
Isla di Elba, Italia
At the core of the drone program is the theory of signature targeting. It is a theory based on the idea that analysts can discern “enemy combatants” from an analysis of outward indicators of patterns of behaviour.
As a practical matter, this approach requires the construction (really a primitive synthesis) of some kind of template describing the universe of behaviour indicators before the fact. In step 2, analysts can compare the observed indicators implicit in a suspected target’s individual behaviour to that predicted by the template. Step three is to make some kind of assessment — usually a subjective probabilistic calculation — of whether or not the target is a valid target. The calculation is subjective because the indicator is based on an array of assumptions buried deeply in the template.
In its more sophisticated — read pseudo scientific — incarnation, the comparison can be done mathematically on a computer using artificial intelligence algorithms. Often this effort involves statistics, including sometimes Bayesian statistics, to give the targeting “analyst” an estimate of the statistical ‘confidence’ in the result of the calculation. The mechanistic nature of this approach raises the possibility that millions of data inputs can be analyzed on a machine without human intervention, with the results summarized in a neat powerpoint briefing, and presented to an overworked decision-maker, who does not have a clue about the deeply buried subjective assumptions underpinning seemingly objective nature of the calculations.
The operative word in this application of artificial intelligence theory is “artificial” because a real intelligence appreciation, as the American strategist John Boyd showed, resides in a decision maker’s Orientation. Boyd’s theory of Orientation involves a balanced interplay of an ever-evolving synthesis growing out of many-sided, continuing analyses, which cut into a problem from many different angles. The objective is insure that one’s Orientation matches the ever-changing requirements of the changing and often menacing external environment. I worked closely with Boyd while he was developing these ideas. For readers not familiar with his ideas, my presentation, Evolutionary Epistemology, is a personal interpretation of his basic theory of knowledge generation. The goal is understand how one evolves an adaptable Orientation to support Observations and Decisions that work in changing conditions of the real world. Readers interested in learning more about Boyd’s ideas can find them explicated in Coram, Fallows, Richards, and Ozinga. Boyd’s own words (beware, they are cryptic) can be found in the Boyd Compendium.
Boyd’s theory of Orientation is crucial for understanding why an algorithmic template based artificial intelligence is so stupid, and so easy to game by all sides, for all sorts of nefarious purposes.
When viewed through the lens of Orientation, the template described above is merely a hardwired (non-evolving) Orientation based on a one-sided analysis. The fatal flaw in this conception is fundamental: Template based artificial intelligence schemes confuse analysis with synthesis. (BTW … ‘Connecting the dots’ is a popular phrase making the same mistake — which is the central reason we never seem to be able to connect the dots!)
The confusion of analysis with synthesis in template-based decision making scheme sets the decision maker up for incestuous amplification, which occurs when the preconceptions implicit in the template drive the both the analyst and decision maker to see what he/she wants to see, rather than what is. The epistemological flaw is basic: Logically, the template requires the analyst to know every possible pattern of a target’s behaviour before the fact. The unrealistic assumption of godlike omniscience reduces the subtle problem of target identification to a simple one of comparative analysis (‘observations’ vs. those predicted by the template) and leads naturally to a mechanistic statistical analysis, together (usually) with a determination of acceptable confidence levels.
In the best of worlds, this kind of hard-wired orientation can be true only if the target is too stupid to adapt unpredictably to the changing conditions that threaten its existence — i.e., if the ‘target’ is an unthinking automaton with no incentive to survive or win. But human beings are adaptive, thinking, creative, and therefore unpredictable creatures with a will to live: Already, for example, there are signs some Al Qaeda wannabees are trying to evolve counter-measures to drones — some laughingly simple and sure to be effective — to neutralize what little effectiveness drones might have. (We already know drones are killing too many civilians and producing highly counterproductive grand-strategic blowback effects).
No doubt, at this point some readers may be wondering where I am going with mumbo jumbo about the mindlessness of confusing synthesis (and creativity) with analysis (and predictability). Well, I urge you to read carefully this important McClatchy report by the inestimable Jonathan Landry. Landry explains in mind numbing detail how you and every American are now in the process of being ‘templated’ by your neighbors and coworkers. Landry shows how your friends and colleagues are being enlisted to feed indicators into the crosshairs of unseen templates concocted by anonymous, mindless, artificial intelligence apparachiks in the Federal Government and their privatized accomplices in industry, all of whom are cashing in on the self-organizing politics of money in a cultural evolution that depends on a compliant American citizenry, anesthetized by fear.
Welcome to the Amerikan Deep State, presided over by the most superficially attractive president since John Kennedy, where signature targeting is coming home to roost in your living room, brought to you by the not-so-creative geniuses in NSA, Microsoft, DOD, DHA, Booz-Allen, etc.
Franklin “Chuck” Spinney is a former military analyst for the Pentagon and a contributor to Hopeless: Barack Obama and the Politics of Illusion, published by AK Press. He be reached at chuck_spinney@mac.com
Experts: Obama’s plan to predict future leakers unproven, unlikely to work
BY JONATHAN S. LANDAY AND MARISA TAYLOR
MCCLATCHY WASHINGTON BUREAU, Miami Herald Nation, 9 July 2013
WASHINGTON — In an initiative aimed at rooting out future leakers and other security violators, President Barack Obama has ordered federal employees to report suspicious actions of their colleagues based on behavioral profiling techniques that are not scientifically proven to work, according to experts and government documents.
The techniques are a key pillar of the Insider Threat Program, an unprecedented government-wide crackdown under which millions of federal bureaucrats and contractors must watch out for “high-risk persons or behaviors” among co-workers. Those who fail to report them could face penalties, including criminal charges.
Obama mandated the program in an October 2011 executive order after Army Pfc. Bradley Manning downloaded hundreds of thousands of documents from a classified computer network and gave them to WikiLeaks, the anti-government secrecy group. The order covers virtually every federal department and agency, including the Peace Corps, the Department of Education and others not directly involved in national security.
Under the program, which is being implemented with little public attention, security investigations can be launched when government employees showing “indicators of insider threat behavior” are reported by co-workers, according to previously undisclosed administration documents obtained by McClatchy. Investigations also can be triggered when “suspicious user behavior” is detected by computer network monitoring and reported to “insider threat personnel.”
Federal employees and contractors are asked to pay particular attention to the lifestyles, attitudes and behaviors – like financial troubles, odd working hours or unexplained travel – of co-workers as a way to predict whether they might do “harm to the United States.” Managers of special insider threat offices will have “regular, timely, and, if possible, electronic, access” to employees’ personnel, payroll, disciplinary and “personal contact” files, as well as records of their use of classified and unclassified computer networks, polygraph results, travel reports and financial disclosure forms.
Over the years, numerous studies of public and private workers who’ve been caught spying, leaking classified information, stealing corporate secrets or engaging in sabotage have identifiedpsychological profiles that could offer clues to possible threats. Administration officials want government workers trained to look for such indicators and report them so the next violation can be stopped before it happens.
TSA officers watch for suspicious behavior at airports (Carey Wagner/Sun Sentinel/MCT)
“In past espionage cases, we find people saw things that may have helped identify a spy, but never reported it,” said Gene Barlow, a spokesman for the Office of the National Counterintelligence Executive, which oversees government efforts to detect threats like spies and computer hackers and is helping implement the Insider Threat Program. “That is why the awareness effort of the program is to teach people not only what types of activity to report, but how to report it and why it is so important to report it.”
But even the government’s top scientific advisers have questioned these techniques. Those experts say that trying to predict future acts through behavioral monitoring is unproven and could result in illegal ethnic and racial profiling and privacy violations.
“There is no consensus in the relevant scientific community nor on the committee regarding whether any behavioral surveillance or physiological monitoring techniques are ready for use at all,” concluded a 2008 National Research Council report on detecting terrorists.
“Doing something similar about predicting future leakers seems even more speculative,” Stephen Fienberg, a professor of statistics and social science at Carnegie Mellon University in Pittsburgh and a member of the committee that wrote the report, told McClatchy.
The emphasis on individual lifestyles, attitudes and behaviors comes at a time when growing numbers of Americans must submit to extensive background checks, polygraph tests and security investigations to be hired or to keep government or federal contracting jobs. The U.S. government is one of the world’s largest employers, overseeing an ever-expanding ocean of information.
While the Insider Threat Program mandates that the nearly 5 million federal workers and contractors with clearances undergo training in recognizing suspicious behavior indicators, it allows individual departments and agencies to extend the requirement to their entire workforces, something the Army already has done.
Training should address “current and potential threats in the work and personal environment” and focus on “the importance of detecting potential insider threats by cleared employees and reporting suspected activity to insider threat personnel and other designated officials,” says one of the documents obtained by McClatchy.
The White House, the Justice Department, the Peace Corps and the departments of Health and Human Services, Homeland Security and Education refused to answer questions about the program’s implementation. Instead, they issued virtually identical email statements directing inquiries to the Office of the Director of National Intelligence, declined to comment or didn’t respond.
Caitlin Hayden, a spokeswoman for the White House National Security Council, said in her statement that the Insider Threat Program includes extra safeguards for “civil rights, civil liberties and privacy,” but she didn’t elaborate. Manning’s leaks to WikiLeaks, she added, showed that at the time protections of classified materials were “inadequate and put our nation’s security at risk.”
Reply from the National Security Council
Even so, the new effort failed to prevent former National Security Agency contractor Edward Snowden from taking top-secret documents detailing the agency’s domestic and international communications monitoring programs and leaking them to The Guardian and The Washington Post newspapers.
The initiative goes beyond classified information leaks. It includes as insider threats “damage to the United States through espionage, terrorism, unauthorized disclosure of national security information or through the loss or degradation of departmental resources or capabilities,” according to a document setting “Minimum Standards for Executive Branch Insider Threat Programs.”
McClatchy obtained a copy of the document, which was produced by an Insider Threat Task Force that was set up under Obama’s order and is headed by Director of National Intelligence James Clapper and Attorney General Eric Holder. McClatchy also obtained the group’s final policy guidance. The White House, the Justice Department and the Office of the Director of National Intelligence declined requests for both documents, neither of which is classified.
Although agencies and departments are still setting up their programs, some employees already are being urged to watch co-workers for “indicators” that include stress, divorce and financial problems.
When asked about the ineffectiveness of behavior profiling, Barlow said the policy “does not mandate” that employees report behavior indicators.
“It simply educates employees about basic activities or behavior that might suggest a person is up to improper activity,” he said.
“These do not require special talents. If you see someone reading classified documents they should not be reading, especially if this happens multiple times and the person appears nervous that you saw him, that is activity that is suspicious and should be reported,” Barlow said. “The insider threat team then looks at the surrounding facts and draws the conclusions about the activity.”
Departments and agencies, however, are given leeway to go beyond the White House’s basic requirements, prompting the Defense Department in its strategy to mandate that workers with clearances “must recognize the potential harm caused by unauthorized disclosures and be aware of the penalties they could face.” It equates unauthorized disclosures of classified information to “aiding the enemies of the United States.”
All departments and agencies involved in the program must closely track their employees’ online activities. The information gathered by monitoring, the administration documents say, “could be used against them in criminal, security, or administrative proceedings.” Experts who research such efforts say suspicious behaviors include accessing information that someone doesn’t need or isn’t authorized to see or downloading materials onto removable storage devices like thumb drives when such devices are restricted or prohibited.
“If you normally print 20 documents a week, well, what happens if the next week or the following week you have to print 50 documents or 100 documents? That could be at variance from your normal activity that could be identified and might be investigated,” said Randy Trzeciak, acting manager of the Computer Emergency Response Team Insider Threat Center at Carnegie Mellon University’s Software Engineering Institute.
“We’ve come up with patterns that we believe organizations might be able to consider when determining when someone might be progressing down the path to harm the organization,” said Trzeciak, whose organization has analyzed more than 800 cases and works with the government and private sector on cyber security.
But research and other programs that rely on profiling show it remains unproven, could make employees more resistant to reporting violations and might lead to spurious allegations.
The Pentagon, U.S. intelligence agencies and the Department of Homeland Security have spent tens of millions of dollars on an array of research projects. Yet after several decades, they still haven’t developed a list of behaviors they can use to definitively identify the tiny fraction of workers who might some day violate national security laws.
“We are back to the needle-in-a-haystack problem,” said Fienberg, the Carnegie Mellon professor.
“We have not found any silver bullets,” said Deanna Caputo, principal behavioral psychologist at MITRE Corp., a nonprofit company working on insider threat efforts for U.S. defense, intelligence and law enforcement agencies. “We don’t have actually any really good profiles or pictures of a bad guy, a good guy gone bad or even the bad guy walking in to do bad things from the very beginning.”
Different agencies and departments have different lists of behavior indicators. Most have adopted the traditional red flags for espionage. They include financial stress, disregard for security practices, unexplained foreign travel, unusual work hours and unexplained or sudden wealth.
But agencies and their consultants have added their own indicators.
For instance, an FBI insider threat detection guide warns private security personnel and managers to watch for “a desire to help the ‘underdog’ or a particular cause,” a “James Bond Wannabe” and a “divided loyalty: allegiance to another person or company or to a country besides the United States.”
A report by the Deloitte consulting firm identifies “several key trends that are making all organizations particularly susceptible to insider threat today.” These trends include an increasingly disgruntled, post-Great Recession workforce and the entry of younger, “Gen Y” employees who were “raised on the Internet” and are “highly involved in social networking.”
Some government programs that have embraced behavioral indicators have been condemned as failures. Perhaps the most heavily criticized is the Transportation Security Administration’s Screening of Passengers by Observation Techniques, or SPOT, program.
The program, which has cost $878 million and employs 2,800 people, uses “behavior detection officers” to identify potential terrorists by scrutinizing airline passengers for signs of “stress, fear or deception.”
DHS’ inspector general excoriated the program, saying in a May 2013 report, “TSA cannot ensure that passengers at United States airports are screened objectively, show that the program is cost-effective or reasonably justify the program’s expansion.”
Interviews and internal complaints obtained by The New York Times quoted TSA officers as saying SPOT has led to ethnic and racial profiling by emphasizing certain profiles. They include Middle Easterners, Hispanics traveling to Miami and African-Americans wearing baseball caps backward.
Another problem with having employees report co-workers’ suspicious behaviors: They aren’t sure which ones represent security threats.
“Employees in the field are not averse to reporting genuine security infractions. In fact, under appropriate conditions they are quite willing to act as eyes and ears for the government,” said a 2005 study by the Pentagon’s Defense Personnel Security Research Center. “They are simply confused about precisely what is important enough to report. Many government workers anguish over reporting gray-area behaviors.”
Even so, the Pentagon is forging ahead with training Defense Department and contractor managers and security officials to set up insider threat offices, with one company emphasizing how its course is designed for novices.
“The Establishing an Insider Threat Program for Your Organization Course will take no more than 90 minutes to complete,” says the proposal.
Officials with the Army, the only government department contacted by McClatchy that agreed to discuss the issue, acknowledged that identifying potential insider threats is more complicated than relying on a list of behaviors.
“What we really point out is if you’re in doubt, report, because that’s what the investigative personnel are there to do, is to get the bottom of ‘is this just noise or is this something that is really going on?’” said Larry Gillis, a senior Army counterintelligence and security official.
The Army implemented a tough program a year before Obama’s executive order after Maj. Nidal Hasan, a U.S.-born Muslim, allegedly killed 13 people in a 2009 rampage at Fort Hood, Texas. Hasan, who has not gone on trial, has said he was defending the Afghan Taliban.
Gillis said the Army didn’t want a program that would “get people to snitch on each other,” nor did it want to encourage stereotyping.
“We don’t have the luxury to make up reasons to throw soldiers out,” Gillis said. “It’s a big deal to remove a soldier from service over some minor issue. We don’t want to ruin a career over some false accusation.”
But some current and former U.S. officials and experts worry that Obama’s Insider Threat Program could lead to false or retaliatory accusations across the entire government, in part because security officials are granted access to information outside their usual purview.
These current and former U.S. officials and experts also ridiculed as overly zealous and simplistic the idea of using reports of suspicious behavior to predict potential insider threats. It takes years for professional spy-hunters to learn their craft, and relying on the observations of inexperienced people could lead to baseless and discriminatory investigations, they said.
“Anyone is an amateur looking at behavior here,” said Thomas Fingar, a former State Department intelligence chief who chaired the National Intelligence Council, which prepares top-secret intelligence analyses for the president, from 2005 to 2008.
Co-workers, Fingar said, should “be attentive” to colleagues’ personal problems in order to refer them to counseling, not to report them as potential security violators. “It’s simply because they are colleagues, fellow human beings,” he said.
Eric Feldman, a former inspector general of the National Reconnaissance Office, the super-secret agency that oversees U.S. spy satellites, expressed concern that relying on workers to report colleagues’ suspicious behaviors to security officials could create “a repressive kind of culture.”
“The answer to it is not to have a Stasi-like response,” said Feldman, referring to the feared secret police of communist East Germany. “You’ve removed that firewall between employees seeking help and the threat that any employee who seeks help could be immediately retaliated against by this insider threat office.”
CORRECTION: A story about the Obama administration's Insider Threat Program gave the wrong name and title for Deanna Caputo, the principal behavioral psychologist at MITRE Corp.
Related Content
•Obama’s crackdown views leaks as aiding enemies of U.S.
•Reply to McClatchy from Education Department
•Reply to McClatchy from Health and Human Services Department
•Reply to McClatchy from the Peace Corps
•Reply to McClatchy from the Army
•Reply to McClatchy from the NSC
•Reply to McClatchy from the National Security Council
Similar Stories:
•Obama’s crackdown views leaks as aiding enemies of U.S.
•After criticism, Obama officials quietly craft new polygraph policy
•US defends intelligence sweep as same as allies



