Graphic: UN 0 Big Picture View of Global Intelligence with Integrity Supporting Documents Added
#OSE Open Source Everything, Advanced Cyber/IO, Autonomous Internet, Earth Intelligence, Peace Intelligence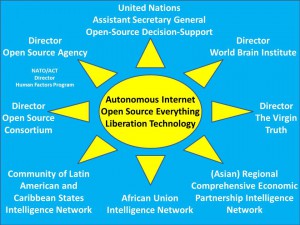
Related Point Papers
Doc (2): Open Source Agency Synopsis 2012
Doc (2): 2012 Reflections on UN Intelligence 2.3 21 Dec 2012
Doc (1): Virgin Truth 2.6
Background Articles
Doc (29): 2012 Reflections on UN Intelligence 2.2 20 Dec 2012
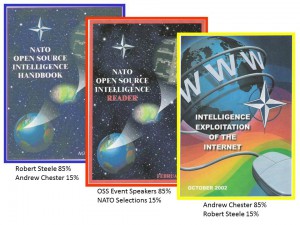
Doc (21): Steele The Craft of Intelligence 3.3
Miscellaneous:
Slide (1): Big Picture
Doc (1): 2013 Public Governance Abstract
Doc (1): Open Source Everything 500 words 1.4
See Also:
2012 THE OPEN SOURCE EVERYTHING MANIFESTO: Transparency, Truth & Trust
2010 INTELLIGENCE FOR EARTH: Clarity, Diversity, Integrity & Sustainability
2008 COLLECTIVE INTELLIGENCE: Creating a Prosperous World at Peace
Yoda: Ten Ways Mobile Learning Will Revolutionize Education
04 Education, Academia, Advanced Cyber/IO, Civil Society, Liberation Technology, Mobile
10 Ways That Mobile Learning Will Revolutionize Education
Fabio Sergio, FastCodeDesign, 20 December 2012
LIST ONLY — Read full article.
1. Continuous learning
2. Educational leap-frogging
3. A new crop of older life-long learners and educators
4. Breaking gender boundaries, reducing physical burdens
5. A new literacy emerges: software literacy
6. Education's long tail
7. Teachers and pupils trade roles
8. Synergies with mobile banking and mobile health initiatives
9. New opportunities for tradtional educational institutions
10. A revolution leading to customized education
Phi Beta Iota: Entire article strongly recommended. We would have added “just enough, just in time learning” but find the over-all list compelling.
2012 Robert Steele: The Human Factor & The Human Environment: Contextual Trust for Sources & Methods
Advanced Cyber/IOCitation: Robert David STEELE Vivas, “The Human Factor & The Human Environment: Contextual Trust for Sources & Methods,” Phi Beta Iota the Public Intelligence Blog (20 December 2012).
This is Part II in a developing conversation highly pertinent to NATO and Allied Command Transformation (ACT).
Robert,
I got that you believe in an intelligence community that is up to the challenge of providing full knowledge and understanding of the environment in support of decision making. This is also my preferred solution. However, I have another human environment issue to solve. The ultimate goal is to influence or shape the human environment. In many cases this implies building trust with people. The problem is that when you approach people with an information collection mindset, you ruin the trust. And when you come with a trust mindset, you don´t get as much information. So, for the sake of trust building, the intelligence community should not be free to interact at will with the people. Could it still do its job under this condition?
Best,
REDACTED
Answer to Question with Graphics Below the Line
Berto Jongman: Building Trust in Cyberspace + Robert Garigue RECAP
Advanced Cyber/IO, Security, Software, SpectrumThe EastWest Institute released Building Trust in Cyberspace, a report featuring highlights of its 3rd Worldwide Cybersecurity Summit held in New Delhi on October 30-31, 2012. More than 300 participants from 22 countries heard from cyber experts from across the globe representing both the private and public sectors.
Open publication | Download (mobile viewing)
Testimonial
I went to a conference that made me rethink everything that I have ever written, said and advocated about the Internet. I had a visceral, emotional reaction to the information presented at the International Youth and Technology Forum on Digital Citizenship, April Rudin – CEO The Rudin Group, The Huffington Post, April 21 2011
IN MEMORY OF ROBERT GARIGUE
He was the first to understand that security is about distributed trust, not centralized control.
See Also:
21st Century Intelligence Core References 2.2
Advanced Cyber/IO: Knowledge Integration
GARIGUE Tagged at Phi Beta Iota
John Robb: Four Sources of Trust, Crypto Not Scaling….
Review: World 3.0 – Global Prosperity and How to Achieve It
Robert Garigue: Feedback for Dynamic System Change
Robert Garigue: Role of the Chief Information Security Officer
Robert Garigue: Security as the Guarantor of Values Executed by Systems–Security as Truth & Trust
Robert Garigue: Standards Toward Interoperability
Robert Garigue: The New Information Security Agenda–Managing the Emerging Semantic Risks
Robert Garigue: The Next Long Wave of Innovation
Robert Garigue: Truth & Trust as Security Requirements
Who’s Who in Cyber-Intelligence: Robert Garigue
Worth a Look: Liars and Outliers – Enabling the Trust that Society Needs to Thrive (Bruce Schneier)
David Isenberg: James Howcroft on Making Intelligence Relevant in the 21st Century
Advanced Cyber/IO, Articles & Chapters
Making Intelligence Relevant for the Missions of the 21st Century
Small Wars Journal | December 19, 2012
The international challenges which threaten the security of the United States and our partners in the 21st century are not primarily posed by conventional military forces. Despite the “pivot” toward a conventional peer competitor in Asia, the predominant source of conflict in the 21st century has been and will continue to be driven by events in fragile or failing states. Of the 27 active conflicts in the world today, only one is a traditional interstate war. Due to the forces of globalization, strife and conflict in these regions now can directly impact the security of citizens within our borders. Unaddressed conflict in these regions gives rise to organized crime networks which engage in trafficking of weapons, drugs, people and WMD components. Ethnic violence results in civil wars which often lead to humanitarian catastrophes and refugee migrations. Ungoverned space may result in terrorist sanctuaries and the spread of radical ideologies and beliefs. The most likely deployment mission will not be to engage against a traditional state’s military, but to engage in an unconventional conflict against non-state foes that use asymmetric tactics.
International security organizations and individual nations have various terms and definitions to address the range of possible operations to address security problems in fragile or failing states: Peace Operations, Peace Support Operations or Stability Operations are commonly used terms. The U.S Department of Defense (DOD) describes Stability Operations as: Military missions, tasks, and activities conducted outside the United States in coordination with other instruments of national power to maintain or reestablish a safe and secure environment, provide essential governmental services, emergency infrastructure reconstruction and humanitarian relief (Department of Defense Instruction 3000.05, “Stability Operations,” September 16, 2009, para. 3). Most often, regional security organizations, such as NATO or the African Union, empowered by the legitimacy of a UN Security Council mandate, form the headquarters or nucleus for ad hoc “coalitions of the willing” to carry out these missions. ISAF in Afghanistan, the African Union Mission in Somalia (AMISOM) and the NATO-led coalition operations in Libya are recent examples of this model. Due to the nature of the missions the military, while a major actor, is only one member of a wider interagency, comprehensive, “whole of government” team assembled to address security, governance, humanitarian and economic developmental needs.
There are numerous, complex challenges to producing and disseminating timely, accurate and fused intelligence to support these operations. Each step of the intelligence process must be adapted to meet the evolving needs of commanders, decision makers, soldiers and civilian partners on the ground. In this era of declining defense budgets, what lessons should intelligence professionals be incorporating into training and educational programs to make success more likely during the next deployment to a fragile or failed state? The following eight examples provide some insights to performing well in a complex environment. It is incumbent on leaders to communicate with and empower their intelligence officers to anticipate mission and information challenges. Incorporating aspects of these examples in training and education programs will help to ensure success on the next deployment.
Mike Nelson: Adam Theirer’s Annual Cyberlaw and Info-Tech Policy Book Review
Advanced Cyber/IO, Economics/True Cost, Knowledge
Always useful!
Important Cyberlaw & Info-Tech Policy Books (2012 Edition)
by Adam Thierer on December 17, 2012 · Add a Comment
The number of major cyberlaw and information tech policy books being published annually continues to grow at an astonishing pace, so much so that I have lost the ability to read and review all of them. In past years, I put together end-of-year lists of important info-tech policy books (here are the lists for 2008, 2009, 2010, and 2011) and I was fairly confident I had read just about everything of importance that was out there (at least that was available in the U.S.). But last year that became a real struggle for me and this year it became an impossibility. A decade ago, there was merely a trickle of Internet policy books coming out each year. Then the trickle turned into a steady stream. Now it has turned into a flood. Thus, I’ve had to become far more selective about what is on my reading list. (This is also because the volume of journal articles about info-tech policy matters has increased exponentially at the same time.)
So, here’s what I’m going to do. I’m going to discuss what I regard to be the five most important titles of 2012, briefly summarize a half dozen others that I’ve read, and then I’m just going to list the rest of the books out there. I’ve read most of them but I have placed an asterisk next to the ones I haven’t. Please let me know what titles I have missed so that I can add them to the list. (Incidentally, here’s my compendium of all the major tech policy books from the 2000s and here’s the running list of all my book reviews.)
Phi Beta Iota: A total “WOW.”
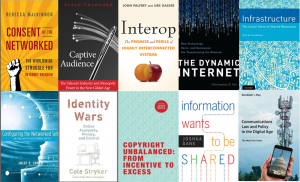
Includes, in this order (click here to read reviews, below to reach Amazon page):
Rebecca MacKinnon – Consent of the Network: The Worldwide Struggle for Internet Freedom
Susan Crawford – Captive Audience: The Telecom Industry and Monopoly Power in the New Gilded Age
John Palfrey & Urs Gasser – Interop: The Promise and Perils of Highly Interconnected Systems
Christopher Yoo – The Dynamic Internet: How Technology, Users, and Businesses are Transforming the Network
Brett Frischmann –Infrastructure: The Social Value of Shared Resources
and others.

