Mike Lofgren Responds to William R. Polk’s, “Intellectual and Political Foundations of 21st Century Jihad.
Mike Lofgren Responds to William R. Polk’s, “Intellectual and Political Foundations of 21st Century Jihad.
My friend, Bill Polk, a distinguished historian specializing in the Middle East, is busily writing a series of extended essays aimed at increasing our understanding of the conflict in Syria and, by extension, our seemingly perpetual war with the Islamic world. I posted the first part of this series, collectively entitled Understanding Syria, on 8 November 2013 here. Attached below is the next essay in the series. More will follow.
I found this essay to be a particularly powerful argument. Those on this list who follow the strategic theories of late Colonel John R. Boyd will find Bill’s analysis of the intellectual/philosophical basis for moral and political cohesion in the first half and the basis of the strategy for Jihad laid out by Abu Bakr Naji (in the last half of the essay) to be entirely consistent with Boyd’s ideas — from grand strategy to tactics. I found the discussion of Jihadist strategy rings lots of Boyd’s bells — particularly those relating to Sun Tzu, Boyd’s critique of Clausewitz’s failure to address the idea of pumping your adversary’s friction to increase his expenditure of effort, his conception of generating non-cooperative centers of gravity, and Boyd’s dissection of insurrection, revolution, and guerrilla war.
What I find to be particularly disturbing about Bill’s analysis is that the counter strategy being pursued by the United States to counter militant Islam fits Naji’s strategy — to paraphrase Eric Von Manstein’s description of the French strategy in 1940 — like a “hand fits a glove.” If you doubt this, think about the nature of our strategic “achievements” in Iraq and Afghanistan.
No doubt, T.E. Lawrence would be smiling ironically at the “Lob-Ottomanization” of U.S. counter-terror strategy.
Readers are feel free to distribute/post Polk's analysis (including my intro if they so desire).
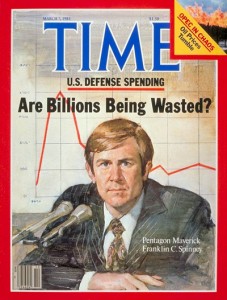
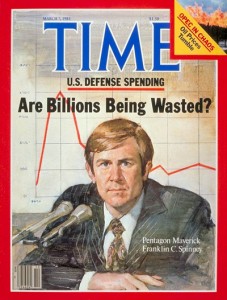
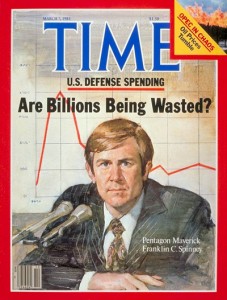
Chuck Spinney
The Intellectual and Political Foundations of 21st Century Jihad
Sayyid Qutub’s Fundamentalism and Abu Bakr Naji’s Jihadism
William R. Polk, December 1, 2013
Technocracy is failed mind control
Whether we know it or not, like it or not, want it or not, we are engaged in a struggle, and that struggle concerns the human spirit—understanding it, experiencing it, defending it against attacks.
The spirit isn’t some vague ghost or apparition. It’s front and center, even in this blind world. It animates action. It has great power. It defies reduction.
The spirit proliferates thought and vision. It doesn’t settle for simplistic harmonies that short-circuit its inventions. It isn’t a happy-happy rainbow. It isn’t a child’s fairy tale.
In articles about my collection, The Matrix Revealed, I’ve stressed, over and over, that human thought originates in a non-material sphere. A sphere outside conventional energy and space and time.
That means the brain isn’t thinking. It’s performing calculations directed by ideas that are far more than chemical/biological reflexes.
Technocracy and its utopian fantasies provide a perfect negative example.
Continue reading “Jon Rappoport; Technocracy as Failed Mind Control”

Stolen Facebook and Yahoo passwords dumped online
The database included details from many of the most popular social networks
More than two million stolen passwords used for sites such as Facebook, Google and Yahoo and other web services have been posted online.
The details had probably been uploaded by a criminal gang, security experts said.
It is suspected the data was taken from computers infected with malicious software that logged key presses.
It is not known how old the details are – but the experts warned that even out-dated information posed a risk.
“We don't know how many of these details still work,” said security researcher Graham Cluley. “But we know that 30-40% of people use the same passwords on different websites.
“That's certainly something people shouldn't do.”
Criminal botnet
The site containing the passwords was discovered by researchers working for security firm Trustwave.
In a blog post outlining its findings, the team said it believed the passwords had been harvested by a large botnet – dubbed Pony – that had scooped up information from thousands of infected computers worldwide.

IC INSPECTOR GENERAL REPORTS ON ACTIVITIES
The latest report from the Inspector General of the Intelligence Community provides an updated (and largely redacted) snapshot of the IG's investigative agenda.
During the nine-month period from July 2012 to March 2013, the IC IG internal hotline received 70 contacts or complaints from intelligence agency personnel, as well as 77 contacts from the general public.
Investigators conducted 75 investigations revealing some occasionally creative forms of misconduct. In one case, an ODNI employee “was operating a personal website on Government time using Government systems through which he solicited and received donations.” Another ODNI employee “attempted to improperly obtain a security clearance for a private citizen through the use of a no-cost contract.”
Three cases of suspected unauthorized disclosures were closed when they were found to be unsubstantiated. Two investigations of unauthorized disclosures remained open as of March 31.
Last month, IC Inspector General I. Charles McCullough III told Congress that his office could not perform an investigation of NSA surveillance programs because it lacked the resources to do so.
“While my office has the jurisdiction to conduct an IC-wide review of all IC elements using these authorities,” Mr. McCullough wrote in a November 5 letter to Senator Leahy and others, “such a review will implicate ongoing oversight efforts. Therefore, I have been conferring with several IC Inspectors General Forum members in order to consider how such a review might be accomplished given the potential impact to IG resources and ongoing projects.”