US Contractors Cited for Syrian Chem Attacks (video)
See Also:

The truth at any cost lowers all other costs — curated by former US spy Robert David Steele.
US Contractors Cited for Syrian Chem Attacks (video)
See Also:

The Immense (and Needless) Human Misery Caused by Speculative Credit Bubbles (August 27, 2013)
Financialization and the Neocolonial Model of credit-based exploitation leave immense human suffering in their wake when speculative credit bubbles inevitably implode.
Discussions of the global financial crisis tend to be bloodless accounts of policy and “growth.” This detachment masks the immense and totally needless human misery created by financial engineering. A correspondent with first-hand knowledge of the situation in Cyprus filed this account:
“RE: the Cyprus economic crisis, the politicians are unbowed by the chaos they caused, still behaving as they have always done, preaching populist platitudes, corrupt as ever, unapologetic. A poll showed that 99% of Cypriots believe their government is corrupt.Yesterday, the former president, Demetris Christofias, appeared before a tribunal investigating the causes of the economic collapse. He tried to force the tribunal to do what he told them, saying, “I am not just any witness, I was the President of the Republic for 5 years”. They told him where to get off and he stormed out.
Little hope for this country. Money leaving. Best talent leaving. Foreign investment in a planned energy hub has been hijacked by the politicians. Cyprus is returning back to what it always was: a tourist destination run by shopkeepers and farmers.Sad days. Most people feel betrayed by the politicians and big powers.”
This report highlights a key dynamic of speculative credit/banking bubbles: they require the complicity of central banks and the state. Speculative bubbles based solely on cash have very short lifespans, as the bubble bursts violently as soon as the gamblers' cash has been sucked into the vortex.
ENHANCING SECURITY THROUGH COLLABORATIVE RESEARCH
Perspectives on Terrorism is a journal of the Terrorism Research Initiative and the Center for Terrorism and Security Studies
Volume 7, Issue 3, pp. 84-98
The Art of Searching: How to Find Terrorism Literature in the Digital Age
This guide provides an overview on information retrieval techniques for locating high-quality literature on terrorism and counter-terrorism. Starting from general considerations on conducting a literature search – taking into account the specifics of terrorism studies – instructions are provided on how to find particular literature types by using different search methods and information retrieval systems, followed by information on how to refine a search by employing focused search strategies. The explanations are enriched with numerous links to recommendable resources. The included examples are focused on terrorism studies, but the general search mechanics can be applied to other research domains as well.
III. Resources
230 Websites and Blogs for Terrorism Research
Compiled and selected by Judith Tinnes
Abstract
This resource collection lists 230 websites and blogs which are deemed to be valuable information sources for serious researchers in the field of (counter-) terrorism studies. The first part lists websites run by academic, governmental, non-governmental, and private institutes, organisations, companies, as well as individual experts. The second part of the collection comprises blogs, many of them containing analyses of primary source materials as well as up-to-date news.
Replicant Hopes to Free Mobile from the Tyranny of Proprietary Software
August 27, 2013
Citing freedom and security concerns, the makers of Replicant are calling for donations, we learn from “Fundraising a Fully Free Fork of Android” at Boing Boing. The project hopes to give us all the choice to run our Android-based mobile devices entirely upon free software.
But wait, you ask, isn’t Android is already open source? Well, most of it, but a few “key non-free parts” keep our Android devices tethered to proprietary programs. Such parts, they say, include the layer that communicates with hardware; yes, that would be pretty important.
Also of concern to Replicant developers are the pre-loaded applications that some of us call “bloatware,” but upon which many users have come to rely. The team plans to develop free software that provides the same functionality. (I hope they also include the option to delete applications without them returning uninvited. That would be a nice change.) Furthermore, they have set up rival to the Google Play store, their app repository called F-Droid. That repository, the article notes, works with all Android-based systems.
The write-up summarizes:
“Mobile operating systems distributed by Apple, Microsoft, and Google all require you to use proprietary software. Even one such program in a phone’s application space is enough to threaten our freedom and security — it only takes one open backdoor to gain access. We are proud to support the Replicant project to help users escape the proprietary restrictions imposed by the current major smartphone vendors. There will still be problems remaining to solve, like the proprietary radio firmware and the common practice of locking down phones, but Replicant is a major part of the solution.”
Replicant is underpinned by copyrighted software that has been released under an assortment of free licenses, which their site links to here. This is an interesting initiative, and we have a couple of questions should it be successful: Will Google’s mobile search revenues come under increased pressure? What happens if Samsung or the Chinese mobile manufacturers jump on this variant of Android? We shall see.
Cynthia Murrell, August 27, 2013
Sponsored by ArnoldIT.com, developer of Augmentext

Pakistan, Taliban and the Afghan Quagmire
With American and NATO combat troops scheduled to depart Afghanistan next year, the relationship between the Afghan Taliban and Pakistan has become more important than ever. It is a complex and complicated nexus. Without doubt, Pakistan and its intelligence service, the Inter-Services Intelligence Directorate of the army (ISI), have more influence over the Taliban than any other country or intelligence service. It provides critical safe haven and sanctuary to the groups’ leadership, advice on military and diplomatic issues, and assistance with fund raising. But its influence is not complete, and whether it could persuade the Taliban to settle for a political settlement in Afghanistan, is unclear at best.
Pakistan’s Support for Survival and Revival of the Taliban
Continue reading “Bruce Reidel: Pakistan Beats USA 12 Years In a Row”
Below is a very important report (all of it below the line), written by Robert Parry, one of the best investigative journalists in what is left of the news business.
As I explained here, the most powerful form of conflict is the M&M strategy waged a the moral level of conflict. The M&M or Motherhood and Mismatch Strategy was conceived by the American strategist, Col. John R. Boyd.
The basic goal of an M&M strategy is to build support for and attract the uncommitted to your cause by framing a “motherhood” position — i.e., a position no one can object to, like the mythical American way of ‘freedom' and ‘democracy' — and then inviting your opponent in to repeatedly attack it and, in so doing, smash himself to pieces at the mental and the even more decisive moral level of conflict. Self-destruction will result inevitably, if you can successfully induce your adversary into attacking your motherhood position in a way that exposes mismatches among the three poles of his moral triangle, defined by (1) What your opponent says he is; (2) What he really is as defined by his actions; and (3) the World he has to deal with.
As Parry shows below, American political and bureaucratic elites are folding the M&M strategy back in on themselves, by fomenting partisan politics, including presidential election politics, that eat away at America's moral triangle from within. The corruption implicit in these politics makes a mockery of the most sacred moral values, including especially those universal ideals we claim apply to the world (and increasingly export via the barrel of a gun).
Left unchecked, an M&M strategy that turns on itself leads inevitably to dissolution and chaos; the only question being its form — perhaps the emergence of a full blown police state from above or a violent revolution from below or some kind of chaotic combination of both.
A CIA Hand in an American ‘Coup'?
By Robert Parry, Consortium News
26 August 13
Special Report: The U.S. government decries leaks, but the other side of the story is that key chapters of American history are hidden from the public for decades and maybe forever. The CIA has just admitted its 1953 Iran coup and may never acknowledge a role in ousting Jimmy Carter in 1980, Robert Parry reports.
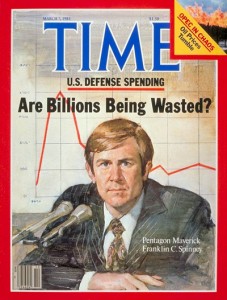
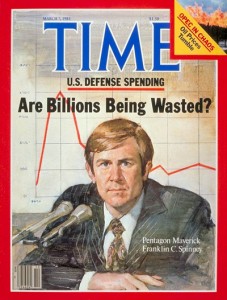
Continue reading “Chuck Spinney: Robert Parry on CIA within CIA Coup Against Jimmy Carler”
The Kosovo Precedent
Syria in the Crosshair
by FRANKLIN C. SPINNEY, Counterpunch, 27 August 2013
http://www.counterpunch.org/
I found it truly scary to read that some high officials in the Obama Administration are so disconnected from reality that they consider the 1999 war in Kosovo to be a precedent for justifying limited cruise missile strikes in Syria.
The inestimable Diana Johnstone ably dissected the illegalities and subterfuges of the Kosovo adventure in numerous articles over the years — her latest being “US Uses Past Crimes to Legalize Future Ones” on 26 August in Counterpunch.
Today, I want to address the stupidity of the Kosovo precedent from a somewhat different angle.
Not only was the Kosovo adventure illegal, it was also a case study in the failure of US precision strike doctrine. One would think the Obama White House would be sensitive to this, because the reasons for the failure are again evident in the metastasizing targets lists governing the conduct of the drone wars in Afghanistan, Pakistan, Yemen, and Somalia.