John T. Fishel
Max Manwaring is one of my heroes, and it upsets me to see the publisher do such a lousy job of posting information about this book, which is a gem. This book was a classic when it was first published, and it is even better now that it has been updated and the SWORD model slightly refined. Along with
The Search for Security: A U.S. Grand Strategy for the Twenty-First Century and Max's other edited work, which I cannot find on Amazon, “Environmental Security & Global Security,” this book is about all any professional needs for a good clear appreciation of how to address low intensity conflicts, complex emergencies, and operations other than war.
The authors understand what Will and Ariel Durant emphasized in their summative The Lessons of History when they said that morality is a strategic value. The heart of this book is about the non-negotiable value of moral legitimacy to govern as the precursor to addressing root problems and preventing terrorism and instability. Winning uncomfortable wars is an IO/psychological and sociological challenge, but you cannot win them, regardless of how much might, money, or message you put on target, if you are not moral in the first place (and if your supported government is not moral).
The other two core messages in this book focus on the urgency of unity of effort across all agencies and the coalition, and the desperate need for LONG-TERM operations with LONG-TERM funding and LONG-TERM commitments from the leaderships of the nations as well as the United Nations and other NGOs. The authors are damning of both the US Congress and the UN for failing to be serious about budgeting for long-term stabilization and reconstruction operations.
The SWORD model has seven parts: unity of effort; legitimacy of the coalition and the supported government; interdiction of support to the belligerents; effective supporting actions by the coalition; military actions by the coalition; interactions between the coalition and the belligerents; and finally, actions tailored to ending the conflict.
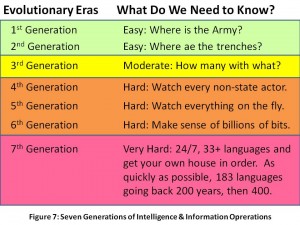
Ambassador Corr could easily be credited with being the third author. His forward provides a sweeping review of history while his conclusion emphasizes that we cannot win without first having “a deep understanding of the cultures and languages…”
A few case studies round out the book. Colombia, where my mother was born, has long been one of Max's special interests. His identification of the three wars (narcos, insurgents, and paramilitaries) reminds me of Tony Zinni's elegant distinctions among the six Viet-Nam wars a) Swamp War, b) Paddy War, c) Jungle War, d) Plains War, e) Saigon War, and f) DMZ War.
Max is far more polite and diplomatic than I am, but his message is clear: US policy is in la-la land when it comes to crop eradication. On pages 197-198 he points out that farmers make four times more from narcotics than from the next available legal crop, and that they are trapped in circumstances where even if they had a profitable legal crop, there is no credit, there are no roads, there is no market, there is no security, for them to evolve legally. Credit, roads, market, security–for the LONG TERM.
Another book that really drives home the ineptitude of our short-term interventions is the one by William Shawcross, Deliver Us from Evil: Peacekeepers, Warlords and a World of Endless Conflict Two other nuanced books I recommend with this one are Robert McNamara and James Blight's Wilson's Ghost: Reducing the Risk of Conflict, Killing, and Catastrophe in the 21st Century and Jonathan Schell's The Unconquerable World: Power, Nonviolence, and the Will of the People.