Michael Jaco on Secret Space Program & Repressed Technologies
Continue reading “Mirror: Super Soldier Talk – Michael Jaco SSP Memories”
Michael Jaco on Secret Space Program & Repressed Technologies
Continue reading “Mirror: Super Soldier Talk – Michael Jaco SSP Memories”
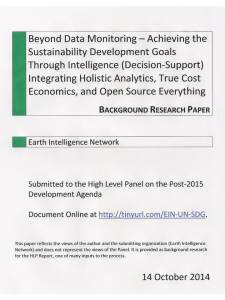 SHORT URL: http://tinyurl.com/EIN-UN-SDG
SHORT URL: http://tinyurl.com/EIN-UN-SDG
Beyond Data Monitoring – Achieving the Sustainability Development Goals Through Intelligence (Decision-Support) Integrating Holistic Analytics, True Cost Economics, and Open Source Everything
BACKGROUND RESEARCH PAPER
Submitted to the High Level Panel on the Post-2015 Development Agenda
DOC (23 Pages): Beyond Data Monitoring 3.4
See Also:
2014 Robert Steele Applied Collective Intelligence
2014 Steele on Intelligence in Ecuador (English)
Translatable Full Text Below the Fold
배 아래에 번역 전체 텍스트
Traduzível texto completo abaixo da dobra
النص الكامل للترجمة تحت طية
翻译全文下方折
Diterjemahkan Full Text bawah Lipat
ਫੋਲਡ ਹੇਠ ਅਨੁਵਾਦ ਪੂਰਾ ਪਾਠ
Перевести Полный текст ниже раза

China's rover leaves first tracks on moon in 40 years
The successful launch marks the next step in an ambitious space program that aims to send a Chinese astronaut to the moon.
BEIJING — China's first moon rover set off slowly Sunday to travel across the right eye of the Man in the Moon, leaving the first wheeled tracks on the moon's surface in nearly 40 years.
No quote emerged to rival “one giant leap for mankind,” but with one loud confirmation by mission control — “the probe landed safely” — China established its status Saturday night as the third nation ever to achieve a “soft-landing” on the moon.
Two weeks after its launch from southwest China, the Chang'e 3 lunar probe, named after a moon goddess, made a careful descent that was reported live on state television. Only the USA and former Soviet Union have previously made soft landings on the moon, whereby the spacecraft and equipment remain intact and operable.
Further celebrations followed Sunday morning as its major cargo, a solar-powered lunar rover named Jade Rabbit after the goddess' pet, rolled down a ramp and set off on a three-month mission to hunt for natural resources and conduct geological surveys.
The Strange Case of Phil Schneider
I don't have the time needed or deserved so I will publish a series of youtube lectures, many are available by Phil Schneider.
Forgotten “Accidented” UFO WhistleBlower Touches Too Close
EXTRACT:
This is where the issue of Phil Schneider comes in. He is a UFO whistleblower who spent his short life saying what was, when he said it, seemed outlandish. We are now putting so many of his 30 year old technologies into use, so many are now public or at least to the advanced defense community that more and more of us accept all of it.

Revolution @State: The Spread of Ediplomacy
Executive summary
The US State Department has become the world’s leading user of ediplomacy. Ediplomacy now employs over 150 full-time personnel working in 25 different ediplomacy nodes at Headquarters. More than 900 people use it at US missions abroad.
Ediplomacy is now used across eight different program areas at State: Knowledge Management, Public Diplomacy and Internet Freedom dominate in terms of staffing and resources. However, it is also being used for Information Management, Consular, Disaster Response, harnessing External Resources and Policy Planning.
In some areas ediplomacy is changing the way State does business. In Public Diplomacy, State now operates what is effectively a global media empire, reaching a larger direct audience than the paid circulation of the ten largest US dailies and employing an army of diplomat-journalists to feed its 600-plus platforms. In other areas, like Knowledge Management, ediplomacy is finding solutions to problems that have plagued foreign ministries for centuries.
The slow pace of adaptation to ediplomacy by many foreign ministries suggests there is a degree of uncertainty over what ediplomacy is all about, what it can do and how pervasive its influence is going to be. This report – the result of a four-month research project in Washington DC – should help provide those answers.
2012-04-03 Hanson_Revolution-at-State (PDF 34 pages)

ROBERT STEELE: Fergus Hanson of Australia has done a truly superb job of describing the considerable efforts within the Department of State to achieve some semblance of electronic coherence and capacity. What he misses–and this does not reduce the value of his effort in the slightest–is the complete absence of strategy or substance within State, or legitimacy in the eyes of those being addressed. If the Department of State were to demand the pre-approved Open Source Agency for the South-Central Campus, and get serious about being the lead agency for public intelligence in the public interest, ediplomacy could become something more than lipstick on the pig. The money is available. What is lacking right now is intelligence with integrity in support of global Whole of Government strategy, operations, tactics, and technical advancement (i.e. Open Source Everything).
See Also:
2012 THE OPEN SOURCE EVERYTHING MANIFESTO: Transparency, Truth & Trust
2012 PREPRINT FOR COMMENT: The Craft of Intelligence
Open Source Agency: Executive Access Point
Preparing America's Foreign Policy for the Twenty-first Century
Review (Guest): No More Secrets – Open Source Information and the Reshaping of U.S. Intelligence
Review: No More Secrets – Open Source Information and the Reshaping of U.S. Intelligence
Robert Steele: Citizen in Search of Integrity (Full Text Online for Google Translate)

[Editor’s note: This is the first in a new column series from the pragmatic visionaries at the Thornburg Center for Professional Development for edtech digest]
“The availability of technologies to youth is its own instructor.” –Nobelist Herbert A. Simon (June 15, 1916 – February 9, 2001), Author of Science of the Artificial and a Father of Artificial Intelligence
EXTRACT: TOYS MIRROR WHAT’S NEXT IN TECHNOLOGY
In the same way that Erector Sets were patterned after the technologies of the third phase of the industrial revolution, the LEGO MindStorms kits reflect the structure of emerging technology and careers in the 21st Century. In 2006, Nano Quest from FIRST Robotics enabled students to program LEGO robots to mimic biological, chemical, and physical systems across micro-, meso-, and nano-scales.
Continue reading “Yoda: Child-Driven Education, Convergence of Knowledge”

I have begun drafting my portion of the new Handbook of Intelligence Studies (Routledge, 2013), it is a chapter early on entitled “The Craft of Intelligence.” I pick up where Allen Dulles and Sherman Kent left off. My graphic on Intelligence Maturity captures the essence of my thinking at the strategic level, but of course there is more to come, including the desperate need to restore integrity to all that we do.
In 1988 I ghost-wrote for the Commandant of the Marine Corps an article that he enhanced and signed, “Global Intelligence Challenges in the 1990's.” At that time my focus was on the difference between the conventional threat and the emerging unconventional threat.
Now my focus is on the purpose and process of intelligence as decision-support. We must — we will — move from secret intelligence for the few to open intelligence for the many; from expensive centralized largely worthless intelligence to free and low-cost distributed intelligence relevant to every person at every level on every issue; from intelligence as window-dressing for channeling $80 billion a year to banks and corporations, to intelligence as an integral element of every aspect of a Smart Nation.
Today Owl sent me a link to an article, Philip E. Tetlock and Barabara A Mellers, “Intelligent Management of Intelligence Agencies,” American Psychologist, 2011, pp. 1-12. I respect Owl, so I printed it and read it twice.
This article is completely out of touch with reality and the authors have not bothered to familiarize themselves with the literatures pertinent to their endeavor. Out of 89 cited sources 12 are non-intelligence-related prior publications of the lead author, 1 is a prior publication of the second author, and 11 are ostensibly about intelligence but truly marginal selections. So 12% sources on the subject, 13% self-citation, and 75% escoteric psycho-babble irrelevant to the actual challenge. As an intelligence professional, I am offended that two ostensibly erudite individuals would dare to publish this trype without even a semblance of understanding of the subject under discussion.
See Also:
Robert Steele: The Craft of Intelligence – OLD vs. NEW
Here are a few comments and additional links: