Stephen E. Arnold: Google Is Not Free
IO Impotency
Are Google and Free an Oxymoron?
I am working on my presentation for the upcoming ISS intelligence conference. One of the topics which I will be addressing is “What is possible and not possible with Google’s Index”
Now don’t get the addled goose wrong. The goslings and I use Google and a number of other online services each day. The reason is that online indexing remains a hit-and-miss proposition. Today’s search gurus ignore the problem of content which is unindexable, servers which are too slow and time out, or latency issues which consign data to the big bit bucket in the back of the building. In addition, few talk about content which is intentionally deleted or moved to a storage device beyond the reach of an content acquisition system. Then there are all-too-frequent human errors which blast content into oblivion because back up devices cannot restore data. Clever programmers change a file format. The filters and connectors designed to index the content do not recognize the file type and put the document in the “look at this, dear human” folder or just skip the file type. And there are other issuers. These range from bandwidth constraints, time out settings, and software that does not work.
SchwartzReport: Ocean Wave Power = Fresh Water Zero Carbon
05 Energy, Earth Intelligence![]() Here is yet another report showing us that if we could emerge from our carbon energy trance there is an entire world of non-polluting energy available to us, as well as a potential freshwater source, which is equally important. Water is destiny. In this, and the next story on Germany, you can see what the transition out of carbon energy looks like when it works.
Here is yet another report showing us that if we could emerge from our carbon energy trance there is an entire world of non-polluting energy available to us, as well as a potential freshwater source, which is equally important. Water is destiny. In this, and the next story on Germany, you can see what the transition out of carbon energy looks like when it works.
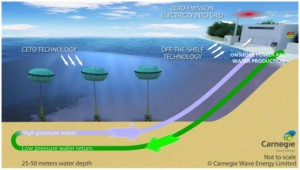
In contrast consider America's insistence on the continuation of carbon energy, most recently through Fracking, whose results are now well-known.
As citizens we must demand that the government focus on noncarbon technologies in service to our interests, as a people, with national wellness as the first priority. It is not the technology but the political will that is lacking. If enough people vote, and make the most compassionate life-affirming decision possible, we can change this. The power of collective intention expressed through voting is a great force.
How The Power Of Ocean Waves Could Yield Freshwater With Zero Carbon Emissions
JEFF SPROSS – Think Progress
NIGHTWATCH: Syria Assad Interview, Other Comments
02 Diplomacy, 03 Environmental Degradation, 04 Inter-State Conflict, 05 Civil War, 05 Iran, 06 Russia, 07 Other Atrocities, 08 Proliferation, 08 Wild CardsSyria: President Asad gave an interview to Le Figaro which was published by the Syrian news agency Sana on 3 September. Excerpts follow.
Asad denied Syrian forces launched a chemical attack. He said Syria has no motive to make such an attack because it is winning the fight. He challenged the US to produce its proof and show it to the UN since the party making the accusations has the burden of proving them.
He said his soldiers were wounded in the attack on the 21st and the UN inspectors visited them in hospital.
He accused the US President of being a weak leader who succumbed to pressure from small groups and as one who starts wars instead of prevents them.
Concerning a Syrian response to a US attack, he reminded the interviewer that the architects of a war only control the first shot. He said the first and the greatest danger is that the situation will explode into a regional war.
In response to a question about Russian support he said,
Continue reading “NIGHTWATCH: Syria Assad Interview, Other Comments”
Bruce Schneier: How Advanced Is the NSA’s Cryptanalysis — And Can We Resist It?
07 Other Atrocities, 11 Society, Corruption, Idiocy, Ineptitude, IO Impotency, Military
How Advanced Is the NSA’s Cryptanalysis — And Can We Resist It?
WIRED Magazine, 09.04.13
The latest Snowden document is the US intelligence “black budget.” There’s a lot of information in the few pages the Washington Post decided to publish, including an introduction by Director of National Intelligence James Clapper. In it, he drops a tantalizing hint: “Also, we are investing in groundbreaking cryptanalytic capabilities to defeat adversarial cryptography and exploit internet traffic.”
Honestly, I’m skeptical. Whatever the NSA has up its top-secret sleeves, the mathematics of cryptography will still be the most secure part of any encryption system. I worry a lot more about poorly designed cryptographic products, software bugs, bad passwords, companies that collaborate with the NSA to leak all or part of the keys, and insecure computers and networks. Those are where the real vulnerabilities are, and where the NSA spends the bulk of its efforts.
See Also:
Continue reading “Bruce Schneier: How Advanced Is the NSA’s Cryptanalysis — And Can We Resist It?”
Berto Jongman: Cyber Security Solutions for the DoD and Intelligence Community
Advanced Cyber/IO, Ethics, IO Privacy, MilitaryCyber Security Solutions for the DoD and Intelligence Community
At first glance, it appears that the Department of Defense (DoD) and the Intelligence Community (IC) have the same cyber security needs as other large organizations in the commercial world. While this is true to a certain extent, the business rules and requirements are significantly different.
The Federal Government, in general, and the DoD/IC are heavily scrutinized and regulated in terms of acquisition policy. The Federal Acquisition Regulations (FAR) and the applicable DoD regulations (DFAR) are comprehensive, administrative and largely bureaucratic in an attempt to protect the interests of the American taxpayer – Cyber Security Solutions have been affected by this process.
This administrative approach has had an initial negative impact on cyber security effectiveness with state sponsored and agile criminal groups enjoying repeated success. As a result, many DoD/IC agencies are reevaluating their cyber security requirements with a more solutions-oriented strategy.
DoD and IC requirements for an effective cyber system include:
Continue reading “Berto Jongman: Cyber Security Solutions for the DoD and Intelligence Community”
Berto Jongman: Kenneth Roth in Politico – When Will Obama Get SDerious About NSA Reform?
Corruption, Idiocy, Ineptitude, IO Impotency, MilitaryWhen will Obama get serious about NSA reform?
Last week, President Obama met with the five-member review board that he recently appointed to review the National Security Agency’s (NSA) controversial electronic surveillance program. The review board is part of the president’s effort to build confidence in the surveillance program and its respect for privacy rights.
But when Obama speaks about the program, he leaves the impression that its existing privacy protections are sufficient, if only we knew enough to appreciate them. That hardly instills confidence. If the president is serious about fixing the enormous overreach of U.S. surveillance that Edward Snowden helped to highlight, he should take these steps:
First, recognize 4th Amendment protection for our metadata. More than 30 years ago, in a different technological era, the Supreme Court ruled that, unlike the content of our phone conversations, we have no privacy rights in the numbers we call. The rationale was that we share those numbers with the phone company. The intrusion mattered little at the time because if the police wanted to reconstruct someone’s circle of contacts, they had to undertake the enormously time-consuming process of manually linking phone number to phone number.


