Edward Snowden: the whistleblower behind the NSA surveillance revelations
The 29-year-old source behind the biggest intelligence leak in the NSA's history explains his motives, his uncertain future and why he never intended on hiding in the shadows
• Q&A with NSA whistleblower Edward Snowden: ‘I do not expect to see home again'

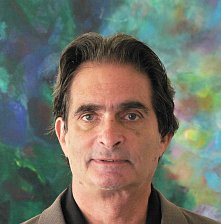
The individual responsible for one of the most significant leaks in US political history is Edward Snowden, a 29-year-old former technical assistant for the CIA and current employee of the defence contractor Booz Allen Hamilton. Snowden has been working at the National Security Agency for the last four years as an employee of various outside contractors, including Booz Allen and Dell.
The Guardian, after several days of interviews, is revealing his identity at his request. From the moment he decided to disclose numerous top-secret documents to the public, he was determined not to opt for the protection of anonymity. “I have no intention of hiding who I am because I know I have done nothing wrong,” he said.
Snowden will go down in history as one of America's most consequential whistleblowers, alongside Daniel Ellsberg and Bradley Manning. He is responsible for handing over material from one of the world's most secretive organisations – the NSA.
In a note accompanying the first set of documents he provided, he wrote: “I understand that I will be made to suffer for my actions,” but “I will be satisfied if the federation of secret law, unequal pardon and irresistible executive powers that rule the world that I love are revealed even for an instant.”