Phi Beta Iota: We take everything with some skepticism. We are quite certain that 95% or more of the U.S. officers training Indonesian military and police personnel had no intention of enabling the atrocities that came later–the problem–as we personally experienced in Central America–is when the 1% to 5%, including personal emissaries from the White House, the Secretary of Defense, and the Central Intelligence Agency all say that there will be no U.S. retribution or blow-back from committing atrocities using US training, equipment, and forms of organization intended to counter bona-fide subversion. Hence, one bad apple rots the entire barrel of good apples.
PART ONE: Cold War and Special Warfare
PART TWO: Camelot and Counterinsurgency
PART THREE: Special Warfare and Low-lntensity Conflict
Philippine Chapter with Highlighted Blue Sections on Lansdale, by Sterling & Peggy Seagrave
See also their books and interview:
Review: Gold Warriors–America’s Secret Recovery of Yamashita’s Gold

British student held over alleged airline bomb attempt
Nigerian man reportedly linked to al-Qaida in custody after foiled terror attempt on transatlantic flight to Detroit
Police identified the suspect as Umar Farouk Abdul Mutallab, 23. It is understood that he is an engineering student at University College London.
One official said the man claimed to have been instructed by al-Qaida to detonate the plane over US soil.
Failed terror attack…Blizzard warning…Fuel spill in Alaskan waters
ROMULUS, Mich. (AP) — Law enforcement and counterterrorism officials say the components of a failed explosive were apparently mixed onboard an international flight bound for Detroit. Passengers subdued a Nigerian man who was apparently burned when the device fizzled, but didn't explode.
WASHINGTON (AP) — U.S. counterterrorism officials are trying to figure out if the failed bombing of an international flight preparing to land in Detroit reveals a serious new threat. Even though it burned but didn't explode, investigators wonder how the mixture allegedly used by a Nigerian man evaded detection
Phi Beta Iota: In the time immediately following 9/11 it was clearly established by multiple parties that our asymmetric opponents were spending $1 for every $500,000 we spent. Today we speculate that the ratio is closer to $1 (them) to $5 million (us). We lack a grasp of reality; we lack a strategy; we lack a force structure; and above all, we lack the moral high ground. Imperial Hubris is what happens when government get “too big to fail” and then promptly collapse because they suffer from a culture that turns disaster into catastrophe. Terrorism is the LEAST of our problems, but for the sake of avoiding argument we accept the United Nations High Level Panel's conclusion that terrorism is number nine out of ten high-level threats to humanity. What we do every day to ourselves is easily a million times more threatening, more costly, and more immoral than anything a single terrorist or terrorist group–whatever their motivations–might do. The BAD DECISIONS made by government are the real sucking chest wound for society, both in terms of perpetuating catastrophic industrial and weather changing practices, and in terms of failing to meet the fundamental needs of people who–if empowered with connectivity and education–would create infinite wealth in every clime and place.
Continue reading “Journal: Hubris Loses to Angst & Reality–Every Time”
Phi Beta Iota: Extremely cool search! Should be combined with a map of Chinese, Turkish, and Brazilian influence in Africa. OSS.Net, Inc. drew on its European allies to provide the tribal maps for Afghanistan and Iraq to Special Forces prior to their going in, and we are still astonished at the complete lack of a serious geospatial mapping capability focused on tribes, influence, and so on.
Let's start with Iran itself. Below is a map of its own divisions.

So when you talk about Iranian influence across Africa, you want to be very clear about both the ethnic roots of the Iranian influence element at point X, and the tribal-ethnic roots of the African element coming into contact with Iranian influence.
We are long over-due for anthropologically-correct maps of the various diasporas, with China, Iran, and Saudi Arabia being among the most important, the latter because of the extreme corruption of their leadership and the extreme virrulence of Wahabbism.
See the graphic on Africa (7) and also, for excellence of depictions, Atlases & State of the World (21).
Articles:
Iran's activity in East Africa
Iran's Activity In East Africa, The Gateway To The Middle East And The African Continent
Cliick on above for a fine report with good detail dated 7 August 2009. The below images come from that report.
The Iranian regime's activities in African countries
Saudis act to counter Iran's influence in the Mideast – Africa & Middle East
The Iranians have been very active in Latin America during the past ten years, at the same time that the Chinese have been using Macao to launch very deliberate campaigns into all former Portuguese territories.

How do I know China wrecked the Copenhagen deal? I was in the room
As recriminations fly post-Copenhagen, one writer offers a fly-on-the-wall account of how talks failed
Copenhagen was a disaster. That much is agreed. But the truth about what actually happened is in danger of being lost amid the spin and inevitable mutual recriminations. The truth is this: China wrecked the talks, intentionally humiliated Barack Obama, and insisted on an awful “deal” so western leaders would walk away carrying the blame. How do I know this? Because I was in the room and saw it happen.
United Nations backtracks on Climategate email scandal, will not investigate

Last week Dr. Rajendra Pachauri, chairman of the UN's Intergovernmental Panel on Climate Change (IPCC), promised an investigation into the Climategate email scandal. Today at a press conference at the United Nations Climate Change Conference (COP15) in Copenhagen, Pachauri backtracked entirely saying, “I want to clarify that this is not an investigation.”
Questions about the impartiality of the various investigations into Climategate had already arisen with many pointing to the corruption that went unfettered in the UN’s ‘Oil for Food’ program. At the time, the UN stymied any attempt to investigate its own program, which generated more than $10 billion in illegal revenue and lined the pockets of many UN officials. Many other UN programs have since been shown to be rife with corruption and scandal.
eople have scoured the exposed CRU emails and compiled all of them into a massive timeline covering 30 years of information contained within, presenting it as a huge PDF. You have to see this to believe it. Look up close and admire the detail while you despair at how long science has been going off the rails.

Download the complete PDF for full detail
.Are you angry about this obvious RICO Act fraud and the national media’s complicity in the cover-up, misinformation, reframing and misdirection of the issue and the related “carbon derivatives” market Obama’s Administration is spinning up? Take responsibility and take action.
STOP all donations to the political party(s) responsible for this fraud. STOP donations to all environmental groups which funded this Global Warming propaganda campaign with our money, especially The Environmental Defense Fund. They have violated the public trust.
By David Talbot
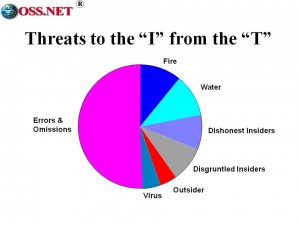
Phi Beta Iota: The story is so good we will not extract from it. It must be read in its entirety. Government is failing to do its job, leaving a “wild west” environment alive and corruptible in the cloud. Standards are beginning to emerge but security is not a priority and the end-user as the ultimate source of the security is not even being considered (over ten years ago Eric Hughes conceptualized anonymous banking and end-user controlled encryption of all data). Eventually, after great expesne and great loss of data, government and industry may realize that the ultimate security is that which originates with the individual end-user, not a central service that can be hacked by disgruntled insiders or that can make a mistake that instantly explodes tens of millions of clients. Below is the original Mich Kabay slide, still relevant.