PDF 39 Pages: 2013-05-23 Fusion Centres – Lessons Learned_ENG
Phi Beta Iota: The report is so narrow as to be virtually useless. What we really need is not lessons from past failures, but rather the embrace of new ideas that cross all boundaries.
PDF 39 Pages: 2013-05-23 Fusion Centres – Lessons Learned_ENG
Phi Beta Iota: The report is so narrow as to be virtually useless. What we really need is not lessons from past failures, but rather the embrace of new ideas that cross all boundaries.
How the U.S. Government Hacks the World
Michael Riley
BloombergBusinessWeek, 23 May 2013
EXTRACT:
The men and women who hack for the NSA belong to a secretive unit known as Tailored Access Operations. It gathers vast amounts of intelligence on terrorist financial networks, international money-laundering and drug operations, the readiness of foreign militaries, even the internal political squabbles of potential adversaries, according to two former U.S. government security officials, who asked not to be named when discussing foreign intelligence gathering. For years, the NSA wouldn’t acknowledge TAO’s existence. A Pentagon official who also asked not to be named confirmed that TAO conducts cyber espionage, or what the Department of Defense calls “computer network exploitation,” but emphasized that it doesn’t target technology, trade, or financial secrets. The official says the number of people who work for TAO is classified. NSA spokeswoman Vaneé Vines would not answer questions about the unit.
The two former security officials agreed to describe the operation and its activities without divulging which governments or entities it targets. According to the former officials, U.S. cyberspies, most from military units who’ve received specialized training, sit at consoles running sophisticated hacking software, which funnels information stolen from computers around the world into a “fusion center,” where intelligence analysts try to make sense of it all. The NSA is prohibited by law from spying on people or entities within the U.S., including noncitizens, or on U.S. citizens abroad. According to one of the former officials, the amount of data the unit harvests from overseas computer networks, or as it travels across the Internet, has grown to an astonishing 2 petabytes an hour—that’s nearly 2.1 million gigabytes, the equivalent of hundreds of millions of pages of text.

LACKFOOT’S PERSPECTIVE ON ZIONISM
Mark Jones’ Crashlist
One of Mark’s [Jones] ideas for the [former “Crashlist”] list, one the moderators share I’m sure, is that the list could be used to share weapons of struggle. Anyone who has done serious mass work, I mean the kind away from the keyboard, knows that sometimes a pithy quote, an uncovered source, an irrefutable fact, a way of phrasing, a piece of reasoning, hypocrisy exposed, an infiltrator outed, a great “expert” really grilled, etc can cause a kind of critical mass and cause all sorts of people from all sorts of backgrounds to take a quantum leap in consciousness or at least take a fork in the road on a whole new direction.
I have been invited several times to debate Zionists on Palestine (usually in the role of a “PalestIndian” as we see Palestinians as the Indians of the Middle East and American Indians as “the Palestinians” of North America). By debatng Zionists, I mean, the official kind, as in working in paid positions for open Zionist organizations clearly tied in with Israel, in the capacity of roving and officially designated “Speakers”. It is Palestinian friends who invite me to join them.
![]() More warnings from the ecosystem.
More warnings from the ecosystem.
Seabird Bones Reveal Changes in Open-Ocean Food Chain
LAYNE CAMERON , PEGGY OSTROM , and ANNE WILEY – Michigan State University
Remains of endangered Hawaiian petrels – both ancient and modern – show how drastically today’s open seas fish menu has changed.
A research team, led by Michigan State University and Smithsonian Institution scientists, analyzed the bones of Hawaiian petrels – birds that spend the majority of their lives foraging the open waters of the Pacific. They found that the substantial change in petrels’ eating habits, eating prey that are lower rather than higher in the food chain, coincides with the growth of industrialized fishing.
The birds’ dramatic shift in diet, shown in the current issue of the Proceedings of the National Academy of Sciences, leaves scientists pondering the fate of petrels as well as wondering how many other species face similar challenges.
‘Our bone record is alarming because it suggests that open-ocean food webs are changing on a large scale due to human influence,” said Peggy Ostrom, co-author and MSU zoologist. ‘Our study is among the first to address one of the great mysteries of biological oceanography – whether fishing has gone beyond an influence on targeted species to affect nontarget species and potentially, entire food webs in the open ocean.”
China-Mali: For the record. China has offered to send more than 500 soldiers to the UN force seeking to contain Islamist militants in Mali . This would be China's largest UN peacekeeping contingent.
Iraq: An attack at a military checkpoint at Taji, north of Baghdad, on Thursday killed 11 people, including four soldiers, and wounded five.
Comment: The pause appears ended. The fighting has killed 420 people this month.
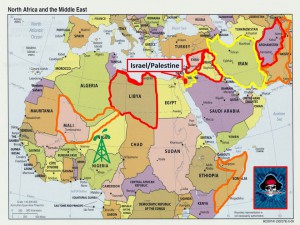
Lebanon: Fighting in Tripoli continued for a fifth day. Overnight clashes killed six people and wounded 40. .The Middle East is now destabilized from the border of Iran to the Mediterranean.
Niger: Islamic militants executed coordinated attacks at two locations in Niger, the country east of Mali. In one attack, a suicide bomber detonated a car bomb at a French-Niger owned uranium mine in the town of Arlit. Simultaneously and 125 miles south, another bomber detonated a car bomb inside a military camp in the city of Agadez. Other jihadists in vehicles attempted to overrun the base, but were stopped by a firefight with Nigerian soldiers. The bombs killed 5 bombers, 25 people and injured 29, according to the Ministry of Defense. No expatriates were killed.
During this Watch, a surviving bomber is holding several Nigerien soldiers hostage
These were the first terrorist attacks of this kind in Niger. The two towns are in central Niger. Some of the facilities for processing uranium ore were damaged at Arlit.
An affiliate of al-Qaida in the Islamic Maghreb, known as the Movement for Unity and Jihad in West Africa (MUJAO) claimed responsibility. They were also involved in the Mali fighting. Nigerien officials judge the fighters came from Libya. One said that Libyan instability is destabilizing the entire region.
Early this year one military analyst judged that Niger was even less prepared than Mali to cope with Islamic militants and terrorists. Nevertheless, a Nigerien unit participated in clearing operations in Gao, Mali.
The key points are that the jihadists have not given up their plans to establish a base in Sahelian Africa and all the countries are vulnerable. Their territory is enormous with poor infrastructure. They are poor and have small, poorly supported security forces.
The attacks might compel France to deploy some of the troops withdrawing from Mali to Niger. Niger is France's single most important supplier of uranium for its extensive nuclear and electric power industries.
France might need to re-evaluate its strategy for providing security assistance to its former colonies. The threat calls for an integrated regional approach to security. The Sahelian nations and France will certainly need outside help.
Phone Data Value And What Companies Are Doing With It
May 23, 2013
Smartphones are an extension of a person’s life and they record it every time a person uses it. Smithsonian Magazine takes a look at how phone companies are tracking and using the data from phones in, “What Phone Companies Are Doing With All That Data From Your Phone.” Verizon Wireless is aware of the phone data goldmine and has added a new division called Precision Market Insights and Telefonica is adding a new business unit Telefonica Dynamic Insights to do the same thing. Phone data is being used for market, medical, and social science research. The biggest usage is tracking how people move in real time. The data collected is supposed to remain anonymous, but that is not happening.
People can be tracked:
“But a study published in Scientific Reports in March found that even data made anonymous may not be so anonymous after all. A team of researchers from Louvain University in Belgium, Harvard and M.I.T. found that by using data from 15 months of phone use by 1.5 million people, together with a similar dataset from Foursquare, they could identify about 95 percent of the cell phones users with just four data points and 50 percent of them with just two data points. A data point is an individual’s approximate whereabouts at the approximate time they’re using their cell phone.”
People’s travel and cell phone patterns are repetitive and unique, making it easy to narrow down results to an individual user. Anonymity is a hard thing to achieve with a smartphone. To confuse the data, a person could get two mobile phones, but then does that increase the fun or increase the risk?
Whitney Grace, May 23, 2013
Sponsored by ArnoldIT.com, developer of Beyond Search

One World, Three Reporting Domains
There are 249 sovereign territories, one sovereign military order, and a few bits of terra nullius that remain unclaimed for obscure reasons. The foreign policy challenges the U.S. faces can be separated into three broad geographic zones – Central & South America, The Muslim World, and the Pacific Rim & Southeast Asia.
I had a good reading background and I spent the first quarter of 2013 focused on The Muslim World. Having sorted out the good news sources and collected a bunch of maps in the process, I determined that simply staying on top of happenings is a full time job. I have not done the same with the other two regions, but I am going to assume that the Pacific Rim & Southeast Asia is roughly the same volume of work, while Central & South America is slightly less busy.