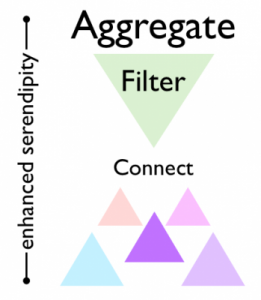
Personal Aggregate, Filter & Connect Strategies
by Jeff Jarvis
A while back my PhD student Sam and I were talking, and he asked me about my RSS feed. His question was something along the lines of ‘what blogs would I have to read if I wanted to be able to make the connections that you do on your blog?’ As we talked, I realised that it didn’t matter if I gave anyone else my exact RSS feed, they wouldn’t be able to replicate my blog – and the reason for this is aggregate, filter and connect.
When I first thought about aggregate, filter and connect as a framework, it was in an attempt to explain why Amazon’s business model worked better than that of other online bookstores. The first time I talked about it in public, it was to explain how open education might work. I’ve been working on making it in to a general model of how we create something unique when we’re primarily dealing with information.
As such, it can be used to explain business models, like Amazon’s, or blogs, like mine. The more I’ve talked about the model, the more other people are picking it up, which is great. Some of these recent discusssions have gotten me thinking about how aggregate, filter and connect works at a personal level. This was really Sam’s question. I’ve talked about how Charles Darwin basically used an aggregate, filter and connect strategy, Phil Long talks about it as part of personal knowledge management, Harold Jarche has discussed it as both a general model for business and for personal knowledge management (an idea that Jack Vinson picked up, and connected to the concept of enhanced serendipity from Ross Dawson), and Glenn Wiebe used the framework to discuss both Joseph Priestly’s inventions and teaching. So we’re starting to get a bit of discussion Today I’d like to illustrate the concept by discussing how I use it.
Phi Beta Iota: Full reading recommended! These folks are redefining both the meaning and the practice of being in harmony with reality, with others, and with relevant information.






 HACKERS ON PLANET EARTH (HOPE)
HACKERS ON PLANET EARTH (HOPE)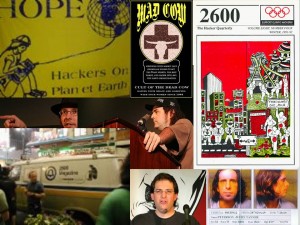 Phi Beta Iota: Hackers are like astronauts, pushing the bleeding edge of the envelope. If the US Government had listened to us in 1991-1994, cyberspace would be secure today, and we would not be spending $12 billion a year on the cyber-scam game–outsourcing to beltway bandits fighting for the 100 folks that actually know how to do this stuff and can qualify for clearances. Our solution for the regional networks is gong to be multinational and open everything. This event is specifically recommended for young teens who show signs of intelligence and curiosity, and for mid-career officers beginning to realize that 80% of what they do is without merit, seeking a better way. This is where we do the right things righter, not the wrong things righter.
Phi Beta Iota: Hackers are like astronauts, pushing the bleeding edge of the envelope. If the US Government had listened to us in 1991-1994, cyberspace would be secure today, and we would not be spending $12 billion a year on the cyber-scam game–outsourcing to beltway bandits fighting for the 100 folks that actually know how to do this stuff and can qualify for clearances. Our solution for the regional networks is gong to be multinational and open everything. This event is specifically recommended for young teens who show signs of intelligence and curiosity, and for mid-career officers beginning to realize that 80% of what they do is without merit, seeking a better way. This is where we do the right things righter, not the wrong things righter.