In the fall of 2010, CACI of Arlington, a major player in the U.S. government's cyber security business, held a symposium entitled “Cyber Threats to National Security,” in partnership with the U.S. Naval Institute to discuss the issue of Cyber Security. CACI is chasing roughly $2 billion worth of cyber-related contracts over the next few years and company executives said they sponsored the symposium pro bono.
The symposium's conclusions: There are redundancies, little coordination and a lack of clarity among the various government agencies, organizations and military command posts that do cyber work. The symposium report notes, “agencies have overlapping and uncoordinated responsibilities for cyber security activities.”
The Obama administration's new Comprehensive National Cybersecurity Initiative (CNCI), it says, “faces substantial challenges that cannot be overcome unless roles and responsibilities of all key CNCI participants are fully coordinated.” That includes several agencies: “Commerce, Defense, and Homeland Security; the Intelligence Community and other executive branch entities,” all with “various overlapping and potentially competing responsibilities.”
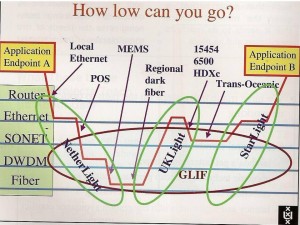
Cybercom under General Alexander is not even going to come close to addressing these problems. Indeed the whole CNCI Program looks increasingly like yet another ploy to grow the U.S. National Security Establishment and spread the government largesse to a new party of contractors. There is no evidence that I have seen that any persons of consequence in the U.S. Government have actually examined the concept of U.S. cyberspace, much less explored methods and techniques that could be employed to provide it with minimum security.
The reason this suggests that the whole CNCI is a scam is that in point of fact that concepts such as ‘cyberspace’ and securing cyberspace have been extensively studied by computer and telecommunications experts in and out of government. No less a government authority than the U.S. National Defense University (a DOD institution) published a detailed and accurate study of these topics in the book Cyberpower and National Security. So the ignorance and confusion over the development of a comprehensive cybersecurity plan on the part of the leaders of the CNCI Program, including General Alexander, is really inexcusable.
That is not to say that the people leading the CNCI are not intelligent, but it is to say they are not serious. They are detached from the real world of cyber threats and information operations and live in a world where all problems are solved by what Robert Steele accurately refers to as contactor vapor ware.