China-Burma: Construction of a high-speed rail link between China's southwestern province of Yunnan and Myanmar will begin in two months. The line will link Kunming, Yunnan's capital to Yangon (Rangoon), on the Indian Ocean, according to Wang Mengshu, an academic from the Chinese Academy of Engineering.
Wang said a China-to-Cambodia high-speed rail connection is under discussion as well as a link between Yunnan and Vientiane, the capital of Laos. He said that all three rail connections are likely to be completed with 10 years. Wang said the project aims to boost cooperation between China and its Southeast Asian neighbors and foster the economic development of China's western regions.
China-Bangladesh: China is interested in increasing cooperation with Bangladesh in different sectors including agriculture technology, trade, commerce and communication, according to a report about the 21 November meeting between Lu Hao, leader of a visiting Chinese delegation and a member of the Communist Party of China and Bangladesh President Zillur Rahman, The Daily Star reported. Rahman called for more Chinese cooperation on socioeconomic development, adding that China is a great friend to Bangladesh. Lu said he hopes the new cooperation will strengthen bilateral relations.
NIGHTWATCH Comment: China is creating a sphere of influence that stretches from North Korea to Pakistan, and surrounds India. This is a threat to US interests as well as to the political independence of the states accepting Chinese aid. A rail line to the Burmese port of Rangoon would give China access to two Indian Ocean ports with direct rail links to China. The other will be Gwadar in western Pakistan which was built with Chinese investments and aid.
Rail links from China through the Karakoram Range to Pakistan Rail and then a spur to Gwadar are undergoing feasibility studies. The link to Rangoon is much more advanced.
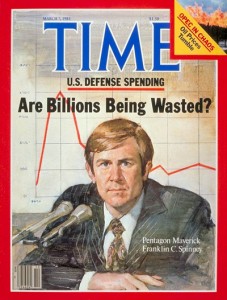
Phi Beta Iota: We must disagree with our learned colleague whose analytic skills we greatly admire. China's building of infrastructure to the seas is not a threat to American the Beautiful as envisioned by our Founding Fathers–it is only a threat to a predatory imperialist out of control government stupid enough to spend $750 million dollars EACH on three fortresses in Baghdad, Kabul, and Islamabad, at the same time that US infrastructure and US economic competitiveness has been DESTROYED by a two-party tyranny that has sold the American public out–in a word, treason against the public interest. ENOUGH. It is time to shut down the Empire before the Empire shuts down America the Beautiful. Tomorrow we will post a review of Buckminster Fuller's Ideas and Integrities written in 1928. He nailed it. The US Government at the political level is NOT in “friendly” hands….certainly not friendly to the 90% that actually pay their taxes unmindful of how those taxes are funding fraud, waste, and abuse on a global scale. America desperately needs an honest President willing to sponsor Electoral Reform in February in time for the 4th of July recall of anyone who votes against it, and a Director of National Intelligence (DNI) who actually wants to create a Smart Nation and stop going along with $90 billion a year in fraud, waste, and abuse….[less the 4% that General Tony Zinni says is useful].