Nobody, anywhere, is doing Open Source Intelligence (OSINT) “right.” There are some nodes where exceptional achievements are the norm in isolation, but by and large, what various governments and corporations are doing and calling “OSINT” is nothing more than very wasteful largely useless Open Source Information (OSIF). At the same time, no consumer is doing Collection Requirements and Evaluation (CRE) and no consumer is holding the secret intelligence world — in any country — accountable for being very expensive and often useless — 4% “at best” of what the Commanding General at US Central Command needed while fighting two wars and 12 Joint Task Forces.
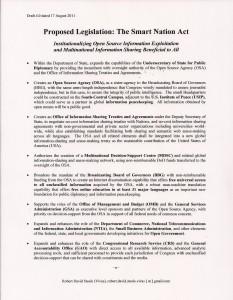
It's time we evolve the craft of intelligence, as I have been advocating for 25 years. I wrote the original OSINT Handbooks for DIA, NATO, and SOF, and am writing a new comprehensive OSINT Handbook for release at my new conference at the McLean Hilton 4-6 December 2017.
Some may have noticed that there is a major programmatic re-evaluation of all OSINT contracts underway. My initial impression is that many option years are at risk, particularly those where management is simply not paying attention and does not understand how unhappy the COTRs are. For a simple flat fee paid in advance I will come in and evaluate any OSINT node in one day, and provide a diagnostic of what's missing and what needs to be fixed to radically reduce risk of the option year not being taken.
Individuals hired as linguists who have no college education and limited experience with digital tools are particularly at risk. The government no longer has the luxury of throwing money around and accepting people because of their language but incapable of understanding a product requirement, designing a research plan, carrying out the research in accordance with the US Army (and other) Open Source Intelligence Handbook precepts, and presenting a finished OSINT product that can be moved into the cloud for sharing with multinational and inter-agency partners.
The US Army, the Special Operations Command, and other elements of the US Government are at the beginning of a complete OSINT program review and program build. In my view, roughly two-thirds of what is being done under CIA precepts that handicap everybody (at the same time that CIA fails to perform effectively in OSINT) should be eliminated, with the savings applied to a completely independent OSINT program funded and owned by DoD but managed in the context of the D3* Innovation Initiative favored by the Secretary of Defense.
As a non-profit educator who is not in competition with any vendor, I am also offering tailored OSINT training that can integrate multiple experts — I have funded over 800 of them over time — in a manner no one else can replicate. Training can be as short as one day and as long as two weeks inclusive of practical exercises on all fronts. Training can be followed with a term of OSINT Help Desk support. This is a contract saver. It can also be used to prep new hires at a cost roughly one tenth the costs of longer programs that teach a great deal that will not be useful and will be quickly forgotten. Think in terms of a $2,500 prep cost versus $10K and up.
The certificate generally reads:
Has completed N hours of virtual online training and N hours of classroom training for a total of NN hours training in Open Source Intelligence (OSINT) support to All-Source Analytics (inclusive of foreign language social media and subject matter expert exploitation utilizing Operations Security (OPSEC) best practices).
The specific methods, tools, official websites, and core references comprising the OSINT Binder are listed. Generally it is the process of OSINT production — including OPSEC — that the individuals have not mastered, the tools are less important — when the client is serious about specific tools they will issue userids and give the contractor analysts a deadline for completing the excellent online training programs that have been paid for as part of the tool purchase agreement.
The other big change in the OSINT world is that most foreign military and law enforcement agencies are finally ramping up their investments in OSINT — EUROPOL just called for all European countries to increase their investments, foreign special operations forces are jumping into this in a big way (and not trusting CIA at all — CIA has lost all credibility in the OSINT arena — its prohibition of overt human contacts by established OSINT cells is criminally insane and mocked by those who see the idiocy of this prohibition). Discussion of a multinational inter-agency intelligence network that is not funded or controlled by the USA has begun. The Chinese, Iranians, and Russian as well as the Turks appear to be seeing that OSINT is the next frontier in Information Operations — not disinformation, but the truth placed before the public, with lies by governments immediately exposed using multi-sourced OSINT. The short-comings of online search are being understood — 80% or more of what we need to know is not secret, not online, not in English, and not accessible without a human path.
I will say for the record that if CIA ever wanted my help, I would gladly assist them. My mistake these past 25 years has been in assuming that CIA might actually be interested in getting it right, I was naive. My focus now is on teaching anyone who wishes to achieve intelligence with integrity by leveraging both Passive OSINT and Active OSINT as well as Black OSINT and Multinational (MNO) OSINT. I see the military as the hub for creating Smart Nations, and foreign militaries working with their own other “tribes” and especially law enforcement, as the center of gravity for the next 25 years.
Starting Points for Reflection
2017 Robert Steele: OSINT Done Right