British student held over alleged airline bomb attempt
Nigerian man reportedly linked to al-Qaida in custody after foiled terror attempt on transatlantic flight to Detroit
Police identified the suspect as Umar Farouk Abdul Mutallab, 23. It is understood that he is an engineering student at University College London.
One official said the man claimed to have been instructed by al-Qaida to detonate the plane over US soil.
Failed terror attack…Blizzard warning…Fuel spill in Alaskan waters
ROMULUS, Mich. (AP) — Law enforcement and counterterrorism officials say the components of a failed explosive were apparently mixed onboard an international flight bound for Detroit. Passengers subdued a Nigerian man who was apparently burned when the device fizzled, but didn't explode.
WASHINGTON (AP) — U.S. counterterrorism officials are trying to figure out if the failed bombing of an international flight preparing to land in Detroit reveals a serious new threat. Even though it burned but didn't explode, investigators wonder how the mixture allegedly used by a Nigerian man evaded detection
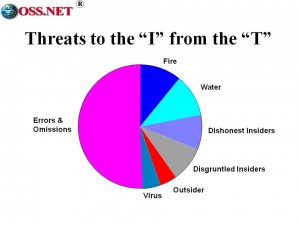
Phi Beta Iota: In the time immediately following 9/11 it was clearly established by multiple parties that our asymmetric opponents were spending $1 for every $500,000 we spent. Today we speculate that the ratio is closer to $1 (them) to $5 million (us). We lack a grasp of reality; we lack a strategy; we lack a force structure; and above all, we lack the moral high ground. Imperial Hubris is what happens when government get “too big to fail” and then promptly collapse because they suffer from a culture that turns disaster into catastrophe. Terrorism is the LEAST of our problems, but for the sake of avoiding argument we accept the United Nations High Level Panel's conclusion that terrorism is number nine out of ten high-level threats to humanity. What we do every day to ourselves is easily a million times more threatening, more costly, and more immoral than anything a single terrorist or terrorist group–whatever their motivations–might do. The BAD DECISIONS made by government are the real sucking chest wound for society, both in terms of perpetuating catastrophic industrial and weather changing practices, and in terms of failing to meet the fundamental needs of people who–if empowered with connectivity and education–would create infinite wealth in every clime and place.
Continue reading “Journal: Hubris Loses to Angst & Reality–Every Time”