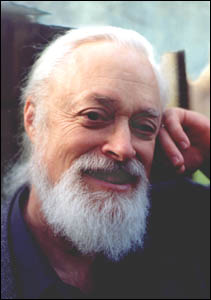
Phi Beta Iota: There is no other person we hold in higher esteem than Tom Atlee. For America the Beautiful, at least, he is this generation's Wise Man. Below in his own words. We urge one and all to contribute to his sustenance.
. . . . . . . . . . . . . . . . . . . . . . . . . .
Dear friends,
I have been talking a lot lately with strategists in the Coffee Party movement (CPM). If you don't know much about the Coffee Party, I urge you to check out their website and Wikipedia's well-referenced short article on them.
While the Coffee Party has definite progressive roots, it also features bright transpartisan energies. Most Coffee Party members — and co-founder Annabel Park — promote civil dialogue about public issues. They also promote democracy-building policies, especially ones to address the democracy-degrading influence of money in politics.
I much prefer the Coffee Party's brand of transpartisanship to the more recent No Labels movement whose goal is “to encourage politicians to come together to develop pragmatic and workable solutions.” Politicians? What about We, the People? What about citizen deliberations and stakeholder dialogues? I can't help but wonder what informed citizen deliberative councils would have to say about the issues the No Labels site addresses…
Although I'm still open to evidence to the contrary, it seems to me that No Labels is trying to co-opt the very real frustration most Americans feel for the political polarization and legislative logjam they see every day. I fear No Labels is cleverly reframing the meme of transpartisanship to rally growing populist energies around a hidden special interest agenda — perhaps building a movement to support a Bloomberg presidential bid in 2012.
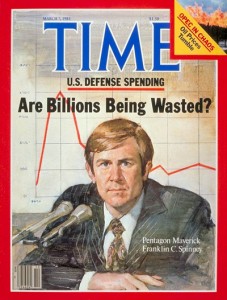
Check out “No Labels: What’s Behind “Forward?” Pro-Corporate Economic Policy.” While I don't agree with everything Jim Cook writes or implies there, I think it is significant that all three No Labels co-founders are professionally involved in promoting corporate interests, and that they advocate tapping Social Security to reduce the debt — when SS is not actually a part of the federal budget, per se, but is a collective retirement account into which workers have paid for decades which has lately been ripped off for budgetary expenditures. Their budget concerns do not highlight the gigantic portion of the actual budget that goes to military expenditures — to say nothing of the non-budgeted expenditures for the wars in Iraq and Iran which constitute a gigantic part of the federal debt — military expenditures that are greater than all other military budgets in the world combined. Nor do they feature the many forms of corporate welfare and the option of raising taxes on the hyper-wealthy to the 1950s levels. Notably, they depend heavily on the Peter G. Peterson Foundation, a very partisan source, as their favorite budgetary reference.
The whole thing doesn't smell right to me. But I do see it as another indicator of how powerful the emerging transpartisan populist trend is, that so much elite attention is being dedicated to co-opting it.