Charges for Soldier Accused of Leak
The New York Times
By STEVEN LEE MYERS
July 6, 2010

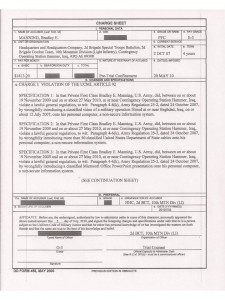
BAGHDAD — An American soldier in Iraq who was arrested on charges of leaking a video of a deadly American helicopter attack here in 2007 has also been charged with downloading more than 150,000 highly classified diplomatic cables that could, if made public, reveal the inner workings of American embassies around the world, the military here announced Tuesday.
Army intelligence analyst charged in Wikileaks case
By Leila Fadel
Washington Post Foreign Service
Wednesday, July 7, 2010
BAGHDAD — The military said Tuesday that it has charged an Army intelligence analyst in connection with the leak of a controversial video and the downloading and transfer of classified State Department cables, in a case that is likely to further deter would-be whistleblowers.
Click on headlines to read each full story.
Phi Beta Iota: PFC Manning swore an oath to defend the Constitutions, not the chain of command and not the secrecy of immoral, illegal, and unaffordable policies that are funded by the U.S. taxpayer and done “in our name” but not at all in our interest. Sunshine is the best disinfectant.
His charge sheet rests on “discrediting the Armed Forces” which is laughable–it is the behavior of our leaders that is a discredit to all of America; and on subverting “good order and discipline.” His behavior in revealing the webs of deceit and incompetence that characterize our military, our “diplomats,” and our spies is precisely what America needs in order to re-establish good order and discipline in harmony with our Constitution.
America needs MORE leaks, MORE “misbehavior,” because we now suffer a “system” that is so far removed from the Founding Fathers' vision, and so deeply divorced from the principles enshrined in our Constitution, that we must, without question, consider PFC Manning to be a “just man” whose best place in a time of injustice is to be in jail as an example to us all. BRAVO ZULU for courage and intelligence in the face of the enemy–he is us. If the lawyer for the defense has any integrity at all, this will be a public jury trial and the PFC will walk free, as he should. It's time to trash this pathological system and get back to the basics of freedom and a foreign policy of commerce and peace.
Wikipedia on Civil Disobedience
Civil Disobedience (Resistance to Civil Government) is an essay by Henry David Thoreau that was first published in 1849. It argues that people should not permit governments to overrule or atrophy their consciences, and that people have a duty to avoid allowing such acquiescence to enable the government to make them the agents of injustice. Thoreau was motivated in part by his disgust with slavery and the Mexican-American War.
Resistance also served as part of Thoreau's metaphor which compared the government to a machine, and said that when the machine was working injustice it was the duty of conscientious citizens to be “a counter friction” (i.e., a resistance) “to stop the machine”.








